Proof of Work vs Proof of Stake: Which is Better?

Key Takeaways
- ⚙️ Proof-of-Work (PoW) secures a blockchain ledger by forcing miners to burn electricity + hardware on solving puzzles; Proof-of-Stake (PoS) secures it by forcing validators to lock capital at risk (stake) and accept slashing.
- ⚙️ Security economics differ (and so do failure modes): PoW attacks require sustained 51% hashpower and ongoing operating spend; PoS attacks require majority stake, but credible misbehavior can trigger on-chain capital destruction and economic finality.
- ⚙️ Energy is the headline divergence: PoW’s energy use is structural (work must be redone every block). PoS makes energy incidental to validation—Ethereum’s shift cut consensus energy use by ~99.95%.
Contents
- 1. Proof of Work & Proof of Stake Definitions
- 2. What is Proof of Work (PoW)?
- 3. Proof of Stake (PoS)
- 4. Key Differences Between PoW and PoS
- 5. Comparison Table: PoW vs PoS
- 6. Similarities Between PoW and PoS
- 7. Security, Risks, and Key Considerations
- 8. Energy Use and Environmental Impact
- 9. Ethereum's Transition to Proof of Stake
- 10. Future of Consensus Mechanisms (2026 Outlook)
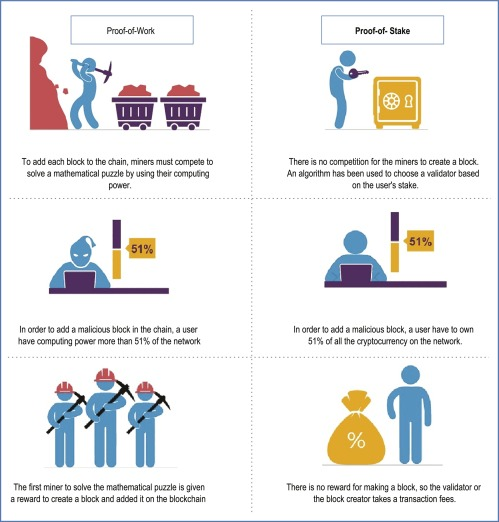
Proof of Work (PoW) and Proof of Stake (PoS) represent two fundamentally different approaches to having blockchain network participants agree on the state of the ledger. Generally, PoW requires miners to solve complex computational puzzles to add new blocks, while PoS selects validators based on the amount of cryptocurrency they lock up as collateral.
The thing is, if one were strictly and definitively better than the other, you wouldn’t need a whole guide dedicated to comparing them. However, in reality, the PoW vs PoS debate is more complex and worthy of discussion, so let’s unpack how they stack against each other.
Proof of Work & Proof of Stake Definitions
Proof of Work (PoW) validates transactions through computational puzzle-solving performed by miners competing for block rewards, while Proof of Stake (PoS) secures networks by requiring validators to lock collateral and earn rewards proportional to their stake. Both consensus mechanisms aim for the same outcome—secure, decentralized agreement on one ledger—but they get there through very different cost models, and that difference cascades into energy use, participation requirements, security assumptions, and performance.
Terms to Know
Source: Chapter Eleven - Cryptographic consensus mechanisms☆☆Introduction to blockchain., Shubhani Aggarwal, Neeraj Kumar, Pethuru Raj, Advances in Computers vol.121 (2021) Before diving into the comparison, revise these six terms that will appear throughout the analysis:
- Consensus mechanism: The protocol that allows distributed nodes to agree on the blockchain's current state without a central authority
- Miner: A network participant in PoW systems who dedicates computational power to solve cryptographic puzzles and validate blocks
- Validator: A network participant in PoS systems who locks cryptocurrency as collateral to propose and verify blocks
- Stake: The amount of cryptocurrency a validator deposits as security, which can be partially or fully forfeited for malicious behavior
- Hash rate: The total computational power miners collectively dedicate to a PoW network, measured in hashes (calculations) per second
- Slashing: The penalty mechanism in PoS that destroys a portion of a validator's stake for rule violations or downtime
What is Proof of Work (PoW)?
Definition
Proof of Work is a consensus mechanism where network participants compete to solve computationally intensive puzzles to earn the right to add new blocks to the blockchain for a reward. At its core, PoW relies on the security assumption that computational power is costly to acquire and deploy, but the results of that computation are trivially easy for other participants, called full nodes, to verify.
As opposed to miners who are specialized participants dedicating computational resources to solving the cryptographic puzzles and proposing new blocks, full nodes, on the other hand, validate proposed blocks by checking that all transactions follow consensus rules and that the proof of work meets the required difficulty threshold.
In simple terms: miners race to find a certain value (number called nonce), broadcasting a solution; nodes worldwide confirm which miner is the winner, the protocol updates the problem and the race continues. This consensus mechanism creates an economically costly barrier to attacks while maintaining a permissionless system where anyone with sufficient hardware and energy can participate in network validation. “Permissionless” puts the emphasis on “anyone” as in “no qualifications or approvals needed”, not necessarily “any setup is fair game” anymore.
How Mining Works

The mining lifecycle in Proof of Work follows a sequence that transforms pending transactions into immutable blockchain history:
- Miners monitor the mempool (memory pool) where unconfirmed transactions wait, selecting which transactions to include based on fee rates and block space constraints.
- Each miner constructs a candidate block containing selected transactions, a reference to the previous block's hash, a timestamp, and other metadata.
- The miner creates a block header that includes a compressed representation of all transactions (Merkle root), the previous block hash, timestamp, difficulty target, and a nonce field. All these references to the previous block are there so there would be a “chain” of “blocks”, as the name implies.
- Then, the miner repeatedly modifies the nonce value and hashes the block header, searching for a hash output that falls below the current difficulty target. This step is the cryptographic “work” in “proof-of-work”.
- Once a valid hash is found, the miner broadcasts the complete block to the network.
- Full nodes across the network receive the block and verify that the hash meets the difficulty requirement and all transactions follow consensus rules. This verification requires only a single hash computation and rule checking—operations that take milliseconds compared to the hours of computational work invested by the miner.
- Nodes update their view of the blockchain to include the new block as the latest addition to the longest valid chain. Rinse, repeat from the start.
Puzzle Solving
The cryptographic puzzle in Proof of Work is often misunderstood. Miners are not “decrypting” anything or solving a mathematical problem with a unique answer. Instead, they are searching for a hash output that meets a threshold condition.
The target-threshold concept works like this: the network sets a difficulty target, which is a numerical value. Miners must find a block header configuration that, when hashed, produces a value numerically lower than the target. They do that by changing the nonce, since other components of a block header remain static. Because cryptographic hash functions produce unpredictable outputs, the process is probabilistic. A miner with more computational power simply gets more attempts per second, which increases the chance of finding a valid hash first—but it never guarantees success on any particular attempt.
Difficulty Adjustment
To maintain consistent block production rates even as miners come and go with their hashing power, Proof of Work systems implement periodic difficulty adjustments. The difficulty adjustment mechanism monitors the actual time taken to produce recent blocks and compares it to the target block interval. If blocks are being produced faster than the target rate, the difficulty increases (target value becomes numerically smaller, making valid hashes harder to find), and vice versa.
Bitcoin, for example, adjusts difficulty every 2,016 blocks based on whether those blocks took more or less than two weeks to produce, targeting roughly 10-minute block intervals.
However, rapid hash-rate changes still create temporary volatility until the next scheduled adjustment. If a large miner or region goes offline, block times can stretch; if new power floods in, block times can shorten. These “lumpy” periods are a tradeoff of discrete adjustment windows, but they smooth out over time.
Block Rewards and Fees

Miner revenue in Proof of Work systems comes from two distinct economic components. The block subsidy (or reward) consists of newly minted coins created with each valid block, representing the protocol's controlled inflation mechanism. Transaction fees, paid by users who want their transactions prioritized, represent the market-driven component of miner income. The total miner revenue for any given block is the sum of the block subsidy plus all transaction fees collected from included transactions, paid out to the miner’s designated block reward address.
This dual-revenue model matters long-term. Block subsidies are often designed to decline over time—either through halvings or other issuance schedules—the importance of transaction fees increases. Thus, networks need robust fee markets so the system can continue funding security when the subsidy becomes smaller.
Bitcoin is the blueprint for this issuance control through a precise mechanism: the network halves the block subsidy every 210,000 blocks, approximately every four years. This predictable reduction schedule caps total Bitcoin supply at 21 million coins while gradually shifting miner incentives from subsidy-dependent to fee-dependent over a century-long transition period.
Examples
Bitcoin remains the canonical Proof of Work implementation. Bitcoin targets roughly 10-minute block intervals. The network halves the block subsidy every 210,000 blocks, creating a deflationary issuance schedule that has produced three halvings since its 2009 launch, with the current subsidy at 3.125 BTC per block. Bitcoin's PoW uses the SHA-256 hash algorithm and represents the largest deployment of computational power in any consensus system, with hash rates exceeding 900 exahashes per second (that’s 995,040,711,197,549,264,896 hashes every second with only one winner).
Litecoin offers a mechanism-level differentiation by implementing the scrypt hash algorithm instead of SHA-256. This design choice was intended to make mining more memory-intensive and less dominated by specialized ASIC hardware, though ASICs eventually emerged for scrypt as well. Litecoin targets 2.5-minute block intervals—four times faster than Bitcoin—and halves its subsidy every 840,000 blocks. Still, with block times four times faster but block height that triggers a halving event four times the Bitcoin’s, the halving schedule and issuance rate for Litecoin is more or less the same as for BTC.
Advantages of Proof-of-Work
Proof of Work provides three distinct mechanism-level advantages that correspond directly to its design properties:
First, objective attack cost: Consensus attacks (collusion) on Proof of Work systems require control of more than 50% of network computational power, a quantifiable economic threshold that scales with honest miner participation.
Second, permissionless participation: Technically, anyone can become a crypto miner by acquiring the necessary hardware and energy access, without requiring approval from existing validators or governance bodies. An open-entry model prevents gatekeeping and allows the network to grow organically as economic incentives attract new participants. Geographic distribution of energy resources naturally promotes decentralization, although at the same time, cheap electricity creates clusters.
Third, simple penalty model: Attempting to attack a PoW network or producing invalid blocks results in wasted computational work and energy costs. Miners who devote resources to mining blocks that the network rejects lose their invested capital and operational expenses without complex governance processes or protocol-enforced penalties. This opportunity cost structure provides a built-in economic deterrent from dishonest behavior.
Disadvantages of Proof-of-Work
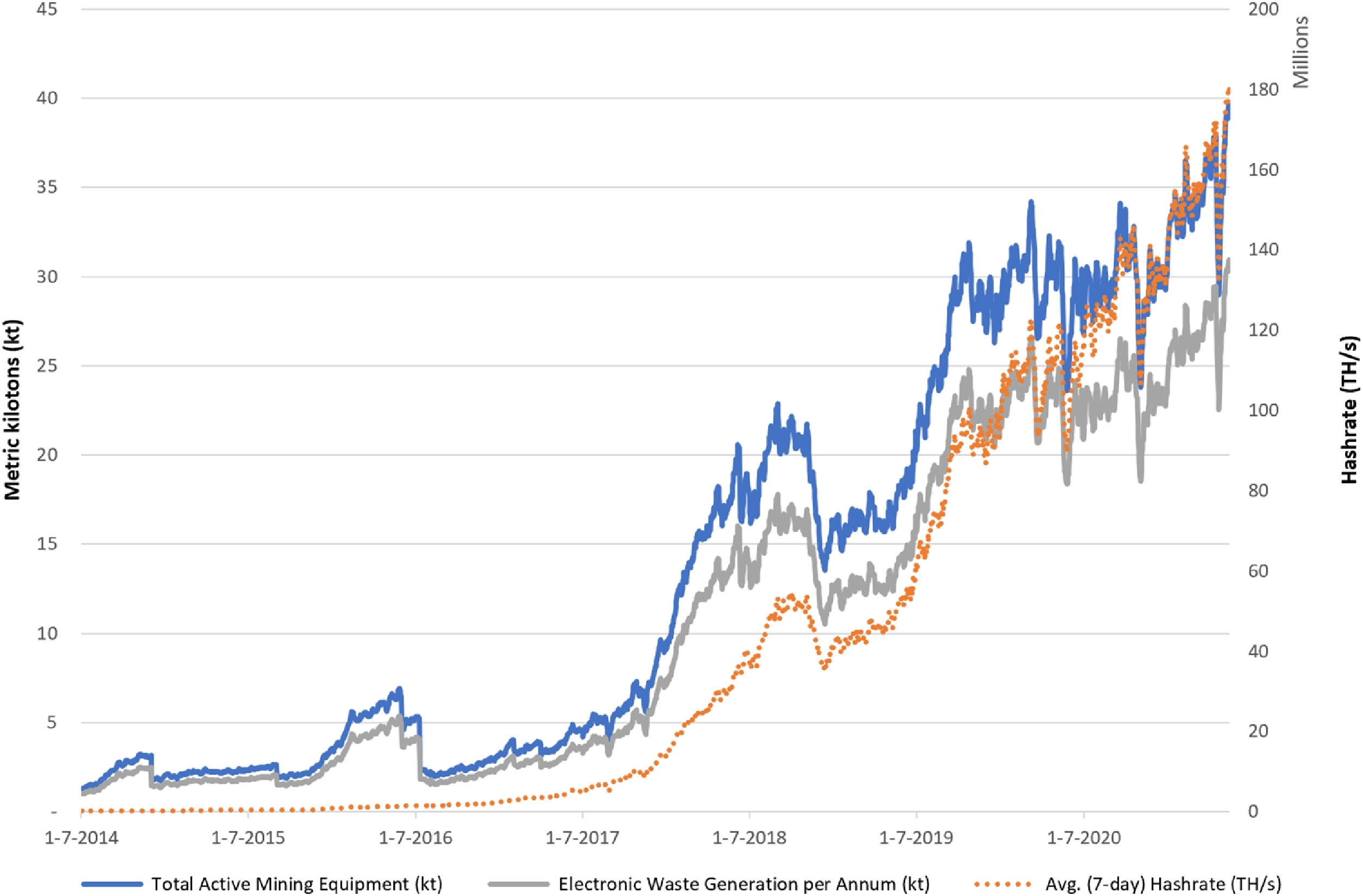
Source: de Vries, Alex; Stoll, Christian (December 2021). "Bitcoin's growing e-waste problem". Resources, Conservation and Recycling. Naturally, this system comes with a number of tradeoffs. Despite its security properties, Proof of Work introduces four specific drawbacks tied to its mechanism:
One, throughput and latency constraints: Block intervals measured in minutes create inherent settlement delays, and the need for blocks to propagate across a geographically distributed network before mining begins on the next block limits practical block sizes. These factors cap transaction throughput and introduce confirmation latency that can't be eliminated without compromising decentralization.
Secondly, miner income variance: Individual miners face high variance in block discovery due to the probabilistic nature of puzzle-solving. A solo miner even with 1% of network hash rate might wait 100 blocks (over 16 hours in Bitcoin) on average to find a single block, creating unpredictable income streams. This variance incentivizes pool formation, where miners combine resources and split rewards proportionally, thus introducing centralization vectors.
Thirdly, hardware arms race: Competition drives continuous investment in more efficient mining hardware, creating economies of scale where larger operations can negotiate better hardware prices and energy contracts. This dynamic favors institutional miners over individual participants, gradually concentrating hash power among entities that can deploy capital at scale.
Additionally, majority attack surface: If an attacker gains majority computational power—controlling more than 50% of total network hash rate—they can engage in transaction censorship, double-spending through chain reorganizations, and prevention of other miners' blocks from being confirmed. Bitcoin makes it prohibitively expensive but for other PoW chains, these attacks are a real threat. While economically irrational for a profit-seeking miner (attacking the network devalues their own mining hardware investment), this security tradeoff represents a fundamental vulnerability in the PoW model that scales with hash rate centralization.
Proof of Stake (PoS)
Definition
At its core, Proof of Stake is a consensus mechanism that selects validators based on their staked tokens, meaning participants must lock up a portion of the network's native coin as a bond before earning the right to propose new blocks, attest to their validity, and finalize transactions. This bonded capital acts like a security deposit: validators who submit invalid data, attempt to manipulate the blockchain, or remain offline risk losing part or all of their stake through automated penalties known as slashing. Or put even more simply, validators put their capital at stake to vouch for the network’s integrity.
The minimum conceptual components that define PoS include: (1) a stake or bond requirement in the network's native token, (2) a rotating validator set chosen via stake-weighted probability, (3) distinct duties (roles) such as proposing blocks, attesting to their correctness, and confirming finality, and (4) economic penalties for protocol violations, which serve as the primary deterrent against attacks.

PoS also gets bundled with other terms that are easy to confuse. “Delegated staking” (DPoS) and “custodial staking” are participation methods within a PoS network but not separate consensus mechanisms. Delegated staking allows token holders to assign their stake to a validator while retaining ownership of keys, whereas custodial staking involves handing control of tokens to a third party (like an exchange) that operates validators on your behalf.
Unlike Proof of Work's reliance on electricity and specialized hardware to verify blocks, PoS achieves consensus through financial commitment—validators face direct monetary penalties for misbehavior, creating security through economic disincentives rather than computational expenditure.
How Staking Works
First, users acquire the network's native token, then lock or bond that stake through a smart contract or protocol-specific interface. From there, participation typically falls into three paths: run a validator node independently (solo staking), delegate stake to an existing validator, or stake via an exchange that pools funds and manages infrastructure.
Solo validators retain full control over their private keys, earn undiluted rewards, and bear full responsibility for uptime and security hygiene. In return, they must meet technical requirements and minimum stake thresholds. For example, Ethereum requires exactly 32 ETH to activate a validator, which translates to a substantial capital commitment at current prices ($74,059.22 at the time of writing). Delegation allows smaller holders to participate by assigning stake to professional validators who handle node operations in exchange for a fee (often 5–20% of rewards). Exchange staking lowers the friction further but introduces custody and counterparty risk: users give up key control, and the exchange becomes the economic actor carrying slashing risk.
Once staked, validators receive protocol duties: assignments to propose blocks, attest to blocks, or participate in consensus checkpoints (of course, the software performs these tasks based on the programming, not the user). Performing these duties correctly earns rewards; neglecting them triggers inactivity penalties. When participants want to exit, many PoS networks impose an unbonding or withdrawal delay (days to weeks), which is designed to keep validators accountable for recent actions rather than letting them disappear instantly.
Validator Selection
Choosing the responsible participant in each round in PoS operates on probability-weighted randomness rather than winner-takes-all competition. Stake size is typically the dominant input: a validator with 10% of bonded stake has about a 10% chance of being chosen to propose the next block.
Most designs add protocol-controlled randomness to prevent complete predictability, which also helps reduce targeted attacks and front-running. Some networks also factor in uptime or availability, favoring consistent validators. Stake age is less common in modern designs because it can reward hoarding rather than active participation.
A core structural concern arising from this design is stake concentration. When a small number of entities controls a large share of stake, they can influence block production and governance. On Ethereum, the top 5% of validators control approximately 70% of total staking power. Such a degree of concentration doesn’t automatically imply an immediate break, but it does raise practical questions about liveness, censorship resistance, and social recovery if the majority acts against minority interests.
Finality
Source: Rhino Bitcoin In PoS, finality is the point at which a transaction becomes extremely unlikely to be reverted—not just included in a block, but confirmed with such strong guarantees that reorganizing the chain would require destroying enormous economic value. This differs from probabilistic finality in Proof of Work, where confidence grows with each additional block but never becomes absolute.
PoS distinguishes between (a) block confirmation, (b) economic finality, and (c) protocol finality checkpoints. The checkpoint mechanism is easiest to picture with a simple example: suppose validators represent 100 units of stake, and the protocol requires 2/3 (67 units) to attest to a checkpoint. Once that supermajority commits, any validator who later tries to build on a conflicting chain can be slashed, making it economically irrational to challenge finalized history.
Slashing
Economic disincentives enforce honest behavior by imposing financial penalties on validators who violate protocol rules. It typically targets equivocation (double-signing), surround votes, and—in some networks—prolonged downtime that threatens liveness.
This is the element that creates the “skin in the game” aspect of staking, although not all systems implement it. By destroying a portion of stake (often 1–50% depending on severity and how many validators are slashed together), PoS aims to make attacks cost more than they can ever return. Inactivity penalties are different: they gradually reduce rewards for validators that go offline, while slashing is immediate and punitive for provable rule violations.
Who bears slashing risk depends on how you participate. Solo stakers carry full exposure. Delegators usually carry proportional exposure if their validator is slashed. Exchange stakers often assume the platform absorbs these risks, but terms of service frequently pass the outcome back to users, meaning a poorly managed validator set can impact customer balances.
Rewards and Fees
Validator rewards in PoS generally come from protocol issuance (similar to block subsidy), transaction fees (including priority fees), and sometimes MEV—Maximal Extractable Value. The balance between these sources shifts with network activity and with how much stake is active: more stake usually compresses APY, while lower participation concentrates rewards among the remaining validators.
Ethereum validators averaged approximately 3.15% APY in Q2 2025, fluctuating with network participation levels, fee market conditions, and validator performance. Delegators receive net returns after validator or exchange fees: a 20% fee on a 5% gross yield leaves 4% net—and over long periods, those differences compound.
Examples of Proof-of-Stake Chains
Ethereum operates a chain-based PoS system after transitioning from Proof of Work via "The Merge" in September 2022, relying on validators who propose blocks and attest to their validity through a combination of Gasper consensus (merging Casper finality with LMD GHOST fork-choice rule).
Cardano uses Ouroboros, a BFT-style PoS protocol with academic research roots, where stake pools produce blocks in proportion to their delegated ADA holdings. BFT stands for Byzantine Fault Tolerance and, without going into much detail, refers to consensus mechanisms resistant to a specific lapse in distributed computing that can undermine the agreement and cause a system collapse.

Photo by Michael Förtsch on Unsplash Polkadot implements Nominated Proof-of-Stake (NPoS), allowing token holders to nominate validators they trust while the network selects the active set algorithmically. Cosmos employs Tendermint BFT consensus, a variant optimized for instant finality and interoperability across independent blockchains. Solana, though often labeled PoS, technically combines voting through Proof of Stake with processing through Proof of History (a cryptographic clock) to achieve high throughput and low latency.
Advantages of Proof-of-Stake
Energy efficiency is PoS’s most visible benefit—validators run lightweight software on consumer hardware rather than industrial mining farms. However, low energy use does not automatically mean a decentralized validator set; stakes can still concentrate.
Lower hardware barriers in comparison to PoW practically broaden participation because validating no longer requires ASICs or massive power contracts. Yet minimum stake thresholds and uptime expectations remain real constraints. 32 ETH is still a high bar even if the electricity bill is negligible.
PoS can also support faster finality than PoW because block production is deterministic and finality gadgets can lock in checkpoints. That said, performance depends heavily on implementation: block sizes, execution limits, and network architecture can still bottleneck PoS chains.
Additionally, economic penalties create a direct enforcement model. In PoW, miners can redirect hardware elsewhere; in PoS, validators risk their bonded stake. This “long-term alignment” is strongest when validators have meaningful capital at risk and doesn’t rely on borrowed stake or opaque structures.
Disadvantages of Proof-of-Stake
Stake concentration is the largest systemic concern of PoS systems and the biggest point of criticism. Large holders tend to accumulate influence via compounding rewards and delegation flows, and this can trend toward oligopolistic control unless mitigated by protocol design and user behavior.
On an architectural level, complexity and implementation risk are also higher for a PoS network. Slashing conditions, finality rules, validator rotations, and inactivity leaks create more moving parts—and more room for subtle failures in edge cases.
Long-range attacks and weak subjectivity are a persistent debate in PoS. If an attacker once held enough stake and later unbonded, they could attempt to rewrite deep history in ways that confuse new nodes syncing from scratch, unless the protocol’s checkpointing and social consensus anchors are applied correctly.
Finally, custodial validator risk is not theoretical. Delegators and exchange stakers take on counterparty and operational security exposure, which changes the risk profile compared to self-custody participation.
Key Differences Between PoW and PoS
By now it is more than clear that these two kinds of systems could not be more different. Although they aim to achieve the same goal—maintaining consensus about the state of the network—their mechanisms are completely different. And yet, none has driven the other to extinction, so let’s clarify what kinds of tradeoffs PoW and PoS systems make and what benefits they prioritize.
Participation

Proof of Work grants validation rights through computational competition. Miners all but must acquire ASICs or high-performance GPUs, secure reliable electricity supplies (often requiring industrial-scale power contracts), and maintain operational uptime to remain competitive. The scarce resource is computational power combined with sustained energy access—both must be spent continuously whether or not a miner successfully produces a block.
Proof of Stake allocates validation rights based on locked capital, allowing participants to become validators by depositing native tokens as collateral. The scarce resource is financial capital that must be staked, not spent but often temporarily illiquid and subject to slashing penalties.
Importantly, running a non-validating full node remains permissionless in both systems, but only staked validators earn protocol rewards and possess block proposal rights, just like miners.
Security Model
Proof of Work secures the network by forcing attackers to acquire and sustain majority hashpower—over 50% of the total computational capacity actively mining the chain. This attack vector externalizes costs: adversaries must continuously pay for electricity, hardware, and facility operations for as long as they wish to maintain control. The punishment mechanism is economic attrition rather than protocol enforcement; honest miners can counter attacks by adding more hashpower or continuing to build on the legitimate chain, eventually outpacing the attacker's resources. If an attack succeeds temporarily, recovery relies on chain reorganization (reorg), where the longest valid chain prevails once the attack ceases.
Proof of Stake protects consensus by requiring attackers to acquire and lock majority stake or exert sufficient influence over delegated validators. The critical difference: stake cannot be easily borrowed or rented without protocol-level mechanisms reacting to abnormal behavior with slashing. Unlike PoW's reorg-based recovery, PoS chains implement economic finality: once a certain threshold of validators attests to a block, it becomes irreversible without massive stake destruction.
The attack-cost intuition differs structurally: PoW attackers need sustained operational control over time (continuously burning resources), while PoS attackers need one-time capital acquisition but then face immediate, automated capital destruction if detected.
Energy Use
Most famously, Proof of Work structurally ties security to continuous energy consumption because validation work must be re-performed in every block interval. Miners compete by executing trillions of hash computations per second, a process that intentionally wastes electricity to establish computational proof that effort was expended. No validator can cheaply simulate work or reuse past computations to claim current rewards. Bitcoin's entire security guarantee rests on the economic cost of sustaining this energy expenditure; removing the energy requirement would eliminate the mechanism preventing costless block production or consensus attacks.
Proof of Stake decouples security from energy by substituting computational work for capital at stake. Signing blocks using cryptographic keys rather than solving puzzles requires negligible electricity compared to hashing, comparable to running a standard server. Validators still consume some energy for hardware operation, network connectivity, and key management infrastructure, but the energy intensity per transaction drops by orders of magnitude.

This reduction applies specifically to consensus mechanisms. On top of consensus, there is an entire application layer: smart contract execution, transaction broadcasting, and node synchronization, which all still consume computational resources, though still far less than mining. PoS shifts the security model from "who can burn the most electricity" to "who has the most capital locked and exposed to risk" making energy consumption incidental to validation rather than fundamental.
Performance
Does the energy expenditure or relative lack of thereof affect network reliability, throughput, speed, scalability? Yes but indirectly.
Proof of Work networks typically exhibit lower throughput and longer time-to-finality due to the probabilistic nature of block production, which implies the need for multiple confirmation blocks to establish practical irreversibility. Bitcoin processes approximately 7 transactions per second (TPS), with users typically waiting for six confirmations (roughly one hour) before considering a transaction settled against deep reorg risk. The block interval is fixed (10 minutes for Bitcoin), and throughput cannot easily scale without altering fundamental security parameters or moving transactions to secondary layers.
Proof of Stake architectures in comparison tend to achieve higher throughput and faster finality through deterministic validator selection and explicit finality mechanisms. Ethereum post-Merge processes over 65 TPS on the base layer. More critically, once a supermajority of validators (typically two-thirds) attest to a block, it becomes finalized. Ethereum's finality occurs in approximately 12-15 minutes under normal conditions—faster practical settlement than Bitcoin's six-confirmation heuristic despite being an explicit, cryptographically enforced guarantee rather than a probabilistic threshold.
From the user’s perspective, PoS can reduce the waiting time expectations for high-value settlements and supports applications that need clear settlement guarantees. The performance advantage stems from replacing energy-intensive proof generation with capital-backed attestations, which enables faster block times and deterministic finality without dropping the security model altogether.
Centralization Risk
Neither PoS nor PoW are completely immune to centralization. Proof of Work concentrates power due to its design incentivizing mining pool formation and incidental ASIC supply chain dependencies. For reference, the top five mining pools control over 80% of Bitcoin's total hash rate, creating single points of failure where pool operators could theoretically coordinate attacks or censor transactions. Geographic centralization compounds this risk: regions with subsidized electricity or favorable regulations attract outsized mining operations, creating geopolitical vulnerabilities. As for ASIC manufacturing, it centralizes control: only a handful of companies produce cutting-edge mining hardware, and supply chain disruptions or regulatory actions can dramatically shift hashpower distribution.
Proof of Stake exhibits stake concentration and custodial validator dominance. Exchanges and staking-as-a-service providers compound this risk by operating large validator sets on behalf of users who delegate their tokens for convenience. As a result, a few entities control vast stake percentages even if representing many individual holders. Unlike PoW's hardware and energy dependencies, PoS centralization stems from capital distribution and the operational complexity of running validators securely.
Hardware Requirements

Similarly to energy requirements, Proof of Work demands specialized hardware optimized exclusively for hash computation, creating a dedicated infrastructure class with limited alternative uses. Modern Bitcoin miners deploy application-specific integrated circuits (ASIC) designed solely for SHA-256 hashing, which become obsolete within 18-36 months as more efficient models emerge. Operating these devices requires industrial cooling systems, stable power delivery infrastructure, and 24/7 uptime to remain competitive. Miners face continuous capital expenditure cycles: purchasing new hardware, disposing of e-waste from deprecated ASICs, and managing physical facilities with significant spatial and thermal requirements.
In comparison, Proof of Stake requires commodity server hardware capable of running a full node and maintaining constant network connectivity, typically a standard server or high-end consumer PC with reliable internet and redundant power. Ethereum validators can operate on modest hardware: e.g., 16GB RAM, 2TB SSD, quad-core CPU. The critical infrastructure becomes key management: validators must secure private keys controlling staked funds, implement redundancy to prevent extended downtime, and ensure signing processes never produce contradictory attestations. Operational risk shifts from hardware depreciation and energy costs to cybersecurity and uptime reliability.
The contrast in hardware requirements reflects each mechanism's core security assumption: PoW externalizes costs through continuous physical resource consumption, while PoS internalizes risk through capital exposure secured by operational discipline.
Economics
Proof of Work compensates miners through block rewards (subsidy plus transaction fees), structured to offset continuous operational expenses. Miners receive revenue only when successfully producing blocks, with income frequency determined (but not guaranteed) by their hashpower share relative to the global network. This reward structure sustains ongoing electricity costs, facility expenses, hardware amortization, and operational labor, functioning as a market-driven subsidy for network security. Issuance rates are typically pre-programmed (Bitcoin's halving schedule, for example), with fees becoming proportionally more important as block subsidies decline over time. The economic incentive aligns security with expenditure: the harder it is to sustain 51% hashpower, the more secure the network.
Proof of Stake rewards validators for locking capital and maintaining operational infrastructure, compensating both the opportunity cost of illiquid stake and the operational risks. Unlike PoW's revenue-minus-expenses model, PoS rewards accrue passively to staked capital with operational costs being relatively minor. Issuance rates often adjust dynamically based on participation: if too little stake is active, rewards increase to attract validators, and vice versa, decrease to prevent excessive inflation. This creates a self-balancing economic mechanism where security (measured in staked value at risk) adjusts based on token issuance and fee revenue, making PoS economics tightly coupled to a network’s broader tokenomics.
Comparison Table: PoW vs PoS
| Dimension | Proof of Work (PoW) | Proof of Stake (PoS) | Why it matters |
|---|---|---|---|
| Participation | Requires specialized mining hardware (ASICs for Bitcoin, GPUs for others) and continuous energy supply to compete | Requires staking minimum amounts of cryptocurrency; can participate through desktop wallets or staking pools | Access threshold varies dramatically—PoW demands upfront capital investment in equipment, while PoS requires locking capital but no specialized gear |
| Security Model | Security scales with cumulative computational work; attackers must outpace 51% of network hashrate continuously | Security scales with economic stake at risk; attackers must acquire and risk losing 51% of staked supply through slashing | PoW security depends on sustained energy expenditure; PoS security depends on capital lock-up and penalty mechanisms—different attack economics |
| Energy Use | Energy-intensive by design; Bitcoin consumes ~120 TWh annually; varies by energy mix used | Drastically lower energy consumption—PoS reduces energy use by over 99% (Ethereum achieved ~99.95% reduction post-Merge) | Environmental impact and operational costs differ by orders of magnitude; regulatory scrutiny increasingly targets high-consumption models |
| Performance | Typically limited throughput—Bitcoin processes ~7 transactions per second; block times fixed by difficulty adjustment (often 10 minutes); transaction speed depends on chain design | Often higher throughput potential—Ethereum post-Merge achieves >65 TPS at base layer; faster finality typically possible; depends heavily on chain design, not consensus alone | Transaction speed and cost vary, but PoS architectures typically allow faster finality and greater throughput; real performance depends on execution layer and L2 solutions |
| Centralization Risk | Pool concentration (top 4 Bitcoin mining pools control ~60% of hashrate) and specialized hardware access create geographic and economic centralization | Stake concentration (top 5% of validators control ~70% of Ethereum stake), custodial validators, and "rich-get-richer" yield dynamics favor large holders | Both mechanisms face decentralization challenges through different vectors—PoW through mining pools and ASIC access, PoS through capital concentration and staking services; centralization risk manifests differently in each |
| Hardware Requirements | Mining-grade equipment mandatory for profitability—ASICs for SHA-256 chains, high-end GPUs for memory-hard algorithms; hardware becomes obsolete as difficulty rises | Standard consumer hardware sufficient; validator nodes require modest specs (16 GB RAM, SSD storage); no specialized chips needed | Lower barriers to technical participation in PoS, but economic barriers (minimum stake amounts) still exist; PoW hardware investment is sunk cost, PoS capital is liquid |
| Economics | Security budget tied to block rewards + transaction fees paid to miners; requires continuous energy/CapEx to maintain; miners can sell rewards immediately; security budget tied to energy/CapEx | Security budget tied to staking yield + fees, offset by slashing risk; validators lock capital opportunity cost; trade-off between liquidity and yield | PoW economics favor operational efficiency and energy access; PoS economics favor capital holders and long-term commitment—different economic incentive structures attract different participant profiles |
| Penalty / Enforcement Mechanism | Sunk costs in hardware and energy create economic deterrent; no protocol-level penalties—miners simply waste resources on invalid blocks | Explicit slashing penalties for malicious behavior or extended downtime; validators lose portion of staked funds; penalties range from minor to complete stake loss | PoS provides direct protocol enforcement against misbehavior, while PoW relies on opportunity cost and resource waste—PoS penalties are more immediate and quantifiable |
| Maturity / Live Examples | Battle-tested since 2009 with Bitcoin; longest-running consensus mechanism; also used by Litecoin, Dogecoin, Bitcoin Cash, and others | Newer at scale; Ethereum successfully transitioned via The Merge in 2022; also used by Cardano, Solana, Polkadot, and newer chains | PoW has proven resilience over 15+ years but faces scaling and sustainability challenges; PoS has demonstrated viability at scale post-Ethereum transition but has shorter track record under adversarial conditions |
Similarities Between PoW and PoS
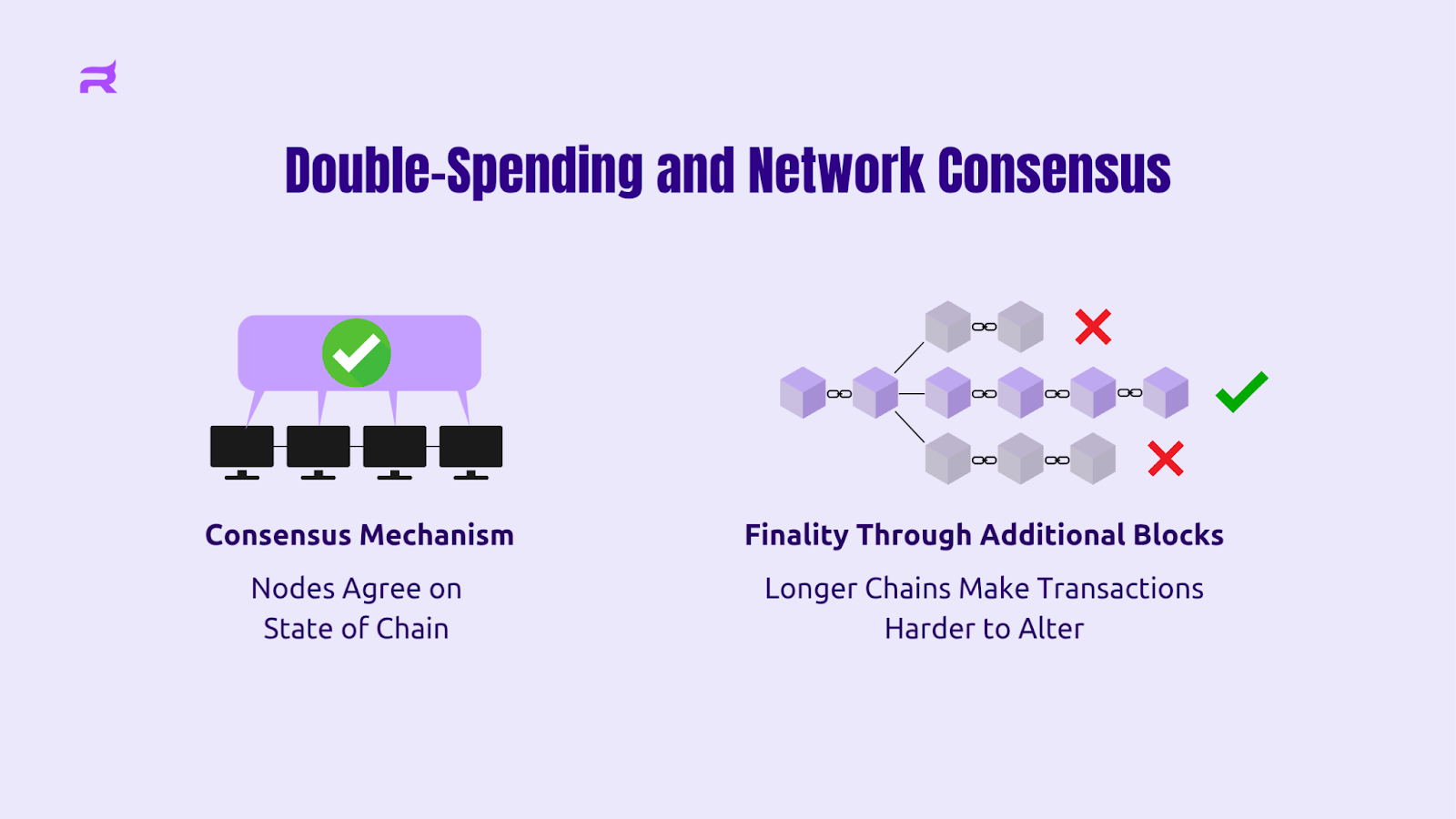
With all that in mind, the common purpose of these systems justifies quite a few similarities in their design. Maintaining the single “true” version of the ledger makes it so that both PoW and PoS need to converge on one canonical chain, key maintainers get rewards for honest behavior, and tampering is economically irrational.
Consensus
Both consensus mechanisms follow a shared workflow. Transactions propagate across nodes. Participants propose candidate blocks. Nodes verify those proposals against protocol rules. Finally, one version of history becomes canonical and the network arrives at the same conclusion.
When competing histories appear, both systems resolve them through protocol-defined convergence rules rather than human intervention. Temporary forks are normal: they can happen when blocks are found at the same time or when network propagation delays blur whose “truth” won. Regardless, over time, both PoW and PoS push the network back toward one shared ledger state.
Incentives
Both models reward correct participation and impose costs for misbehavior. They also create opportunity costs: mining hardware and infrastructure lock capital into a single specialized activity, and staked tokens become illiquid and exposed to penalties. Both rely on protocol rewards plus user-paid transaction fees, and both need functional fee markets to maintain long-run security, especially as issuance schedules evolve.
At the core is the same economic logic: network security holds when the cost to execute an attack exceeds any benefit. That’s the real “double-spend prevention” story in both designs.
Network Integrity
Both models aim for tamper-resistance, auditability, and censorship resistance. If an attacker proposes an invalid block—say, a transaction that spends more tokens than exist—nodes reject it. In PoW, the miner eats the cost in wasted electricity and orphaned work. In PoS, the validator risks slashing if they sign provably invalid data.
Both also depend on practical infrastructure: reliable network connectivity for propagation, correct client software, and enough independent operators so consensus power cannot be quietly captured. Centralization risk exists in both; the difference is where that risk concentrates.
Security, Risks, and Key Considerations
Because there is no entity to mitigate incidents, security in blockchain consensus mechanisms has to compensate. Risks include invalid state transitions, chain reorganizations, and censorship, and in practice, live across three layers at once: protocol design (technical), incentive alignment (economic), and crisis response (social coordination).
Common Attack Vectors
Once you go beyond Bitcoin and Ethereum, attacks on the blockchain’s integrity itself become an increasingly real threat.
51% majority control attacks are the headline risk in both models, but the execution differs. In Proof of Work, majority control means sustained access to more than 50% of the hash rate, which requires hardware and continuous energy burn. In Proof of Stake, majority control means more than 50% of bonded stake and influence over validator behavior. Outcomes overlap—double-spending, censorship, deep reorgs—only the attacker’s cost profile is fundamentally different.
Made possible by the previous threat, censorship attacks happen when miners or validators exclude transactions or addresses. Censorship can be driven by side payments, regulatory pressure, or strategic MEV. Censorship can be expensive to sustain through lost fees, reputational fallout, or slashing risk but not if it is countered by the majority of network participants.
Long-range attacks are unique to Proof of Stake because old keys can, in theory, produce alternate historical chains once stake is no longer bonded. Weak subjectivity is the core issue: a new node can’t always objectively pick the “real” chain without a trusted recent checkpoint. Checkpointing plus slashing rules are standard mitigations, but this remains a meaningful philosophical and operational difference from PoW.
Nothing-at-stake equivocation is another PoS failure mode where validators sign multiple competing blocks because signing is cheap. Slashing is the deterrent: Ethereum 2.0 burns at minimum 1 ETH for simple equivocation and potentially entire stake balances for coordinated attacks. Because signatures are cryptographic proof, equivocation can be detected and punished if the protocol’s slashing design is tight and enforcement is credible.

Sandwich attack. Source: Rileys Substack MEV-related attacks cut across both models. When MEV becomes larger than the block reward, reorg incentives can appear, and rational actors might attempt to orphan blocks to capture the extractable value. In PoW, short reorg incentives are limited mainly by orphan costs; in PoS, validator behavior and relay infrastructure can intensify ordering games.
Economic Costs and Incentive Failures
The economic difference is simple to state but deep in consequences. Proof of Work makes attackers pay in hardware and electricity; Proof of Stake makes attackers pay in capital at risk.
Speaking of MEV, incentive failures appear when short-term profit beats long-term network health. Censorship is another classic example: in PoW, the only direct penalty is lost fee revenue; in PoS, slashing can act as a credible threat, but only if the violation is detectable and enforceable before an attacker can exit.
Cartelization is another risk. If a small group controls a supermajority of consensus power, they can coordinate in ways that disadvantage smaller participants, whether through pool policies in PoW or governance influence and validator cartels in PoS.
Governance and Social Consensus
When protocol defenses fail, social consensus becomes the backstop: a human decision about which chain is considered canonical. The actors influencing these moments are not just developers and validators/miners. Exchanges, stablecoin issuers, major DeFi apps, and end users (each network user) also shape which fork becomes “real” through listings, deposits/withdrawals, and actual usage.
Imagine a scenario: an attacker detected a zero-day bug in a major Proof of Stake network and minted 5% of the total token supply over 72 hours. Within the first six hours, core developers coordinate on Discord and GitHub to diagnose the exploit and draft an emergency patch. By hour 12, they've contacted major validators (representing 80% of stake) to coordinate an upgrade deadline. Hour 18 sees the first social media announcements explaining the situation to users and requesting they halt deposits/withdrawals. By hour 36, exchanges freeze trading, and the development team proposes a hard fork that rewinds the chain to a pre-exploit block, invalidating the attacker's minted coins.

Ben Burns, Amir Bandeali, Alex Xu and Will Warren brainstorming on 0x; Source: Medium In Proof of Work, miners must choose which fork to mine, and incentives can prolong uncertainty. In Proof of Stake, coordination may move faster because validators have bonded capital at risk. But speed introduces a different concern: if history can be rolled back for emergencies, how often will the community accept rollbacks for less objective reasons?
Energy Use and Environmental Impact
One factor that used to occupy a good chunk of the conversation surrounding cryptocurrencies is environmental concerns. Particularly, the exorbitant energy waste and e-waste produced by Proof-of-Work cryptocurrencies such as Bitcoin and Ethereum at the time. Since Ethereum’s transition to PoS, this criticism surfaces less often but still comes up for BTC.
Power Demand and Efficiency
Proof of Work and Proof of Stake differ fundamentally in electricity requirements because of how block producers compete. In PoW networks like Bitcoin, miners continuously run specialized hardware solving cryptographic puzzles at full capacity. Competitive hashing plus industrial-scale hardware maintenance creates constant power demand that scales with network difficulty and miner participation. Ethereum's transition to Proof of Stake, known as The Merge, reduced the network's energy consumption by approximately 99.95%, demonstrating the operational difference between these consensus mechanisms.
Research comparing energy efficiency across blockchain protocols shows that Proof of Stake delivers order-of-magnitude improvements in sustainability over Proof of Work systems, supporting a more sustainable security budget for many use cases.
Emissions
Energy consumption and carbon impact are related but not identical. A simple emissions model is: Electricity consumed (kWh) × Grid carbon intensity (gCO2/kWh, region-dependent) = Emissions (plus optional additions for cooling and construction).
The regional factor is not a footnote. The same PoW hardware can be near-zero emissions on geothermal-heavy grids and high-emissions on coal-heavy grids, which is why blanket conclusions often miss the operational reality. Many PoW operations utilize alternative energy sources, such as the mentioned geothermal, solar, or other renewables; that being said, the primary driver for it is not ecological concerns but rather, cheaper, often subsidized, costs.
E-Waste
Electronic waste, or worn out unrepurposable hardware, follows different pathways in each model. In Proof of Work, ASIC specialization drives faster obsolescence cycles: as difficulty rises and more efficient machines are released, older ASICs can become unprofitable within 18–24 months. To add insult to injury, those chips can’t easily be repurposed because they are designed to do one thing.
In Proof of Stake, validator hardware is commonly general-purpose. When a validator retires a server, the equipment can often be resold, repurposed, or used for non-crypto workloads, extending its lifecycle.
CPU and GPU-mined networks have different lifecycle dynamics than ASIC-dominated mining: after all, unless they are completely worn out, GPUs do retain some resale value. However, the market share of these networks is much smaller than Bitcoin’s and PoS networks, so they are often left out of the conversation entirely.
Ethereum's Transition to Proof of Stake
The PoW vs PoS debate often comes up when discussing Ethereum’s history; after all, it is the most prominent example of a blockchain network switching consensus algorithms. Ethereum completed The Merge in September 2022, fundamentally changing how the network validates transactions while maintaining continuity for existing users and applications. The transition replaced energy-intensive mining with validator-based consensus, yet preserved every account, smart contract, and transaction history.
Timeline

The path from announcement to execution spanned multiple years of research, testing, and staged deployments, with each milestone addressing specific technical and economic challenges:
- 2020–2021: Beacon Chain Launch – Ethereum introduced a parallel Proof of Stake chain to run alongside the existing Proof of Work mainnet, allowing validators to begin staking ETH and testing consensus mechanics without affecting live operations, which de-risked the eventual merger by proving the PoS model could handle real economic value.
- September 15, 2022: The Merge – The original PoW execution layer unified with the Beacon Chain, instantly transferring block production duties from miners to validators and eliminating mining entirely, which preserved all existing infrastructure (wallets, dapps, exchanges) while fundamentally altering the security model.
- 2022–2023: Validator Growth Phase – Participation surged from initial early adopters to hundreds of thousands of active validators, demonstrating that even the steep 32 ETH staking requirement attracted sufficient decentralized participation.
- April 2023: Shanghai Upgrade – Ethereum enabled staked ETH withdrawals for the first time, removing the "one-way door" constraint that had locked validator funds since the Beacon Chain's inception.
A common misconception is that the change was motivated by criticisms of blockchain’s environmental impact, which in early 2020s was a major part of the discourse. In reality, the transition was planned from the very beginning of Ethereum’s history.
Practical Implications
- Stakers and Validators: Returns follow a dynamic issuance curve, and uptime becomes a core responsibility. Fractional access often comes through liquid staking derivatives.
- Dapp Users: Block times (~12 seconds) and gas fees didn’t change just because consensus changed. The Merge was consensus-only; scaling and fee relief remain execution and Layer 2 topics.
- Security Watchers: Attack costs shifted from hashrate acquisition to staked ETH control and slashing exposure, while validator concentration makes censorship/regulatory capture a more realistic concern than a “pure” chain takeover.
- Long-Term Holders: Staking has created a native yield path for ETH, but many participants still choose liquid staking tokens, which adds smart contract and counterparty dependencies.
- Ecosystem Observers: Concentration in custodial and liquid staking services can create coordinated failure or compliance pressure points, directly touching credible neutrality.
Future of Consensus Mechanisms (2026 Outlook)
Most feasibly, consensus mechanisms will bifurcate into specialized roles, with Proof of Stake dominating general-purpose Layer 1 and Layer 2 ecosystems for scalability and energy efficiency, Proof of Work persisting in value-storage and censorship-resistant niches where externalized cost justifies energy trade-offs. Hybrid models emerge to solve edge-case security and finality requirements that neither pure mechanism addresses alone.
Hybrid Models
Hybrid consensus architectures combine components from different validation mechanisms to exploit their complementary strengths while attempting to neutralize their individual weaknesses.
PoS Block Production + BFT Finality uses PoS validators for rapid block production and BFT algorithms (Tendermint, HotStuff) for instant finality. The benefit is deterministic finality with PoS-level energy efficiency, while the risk is that BFT communication demands can push systems toward smaller, more coordinated validator sets.
PoW Leader Election + PoS Checkpoints uses PoW for proposer selection and PoS signatures for periodic checkpoints. This preserves PoW’s externalized Sybil resistance while reducing deep reorg risk, but it adds complexity and creates new coordination failure modes if miners and stakers diverge during partitions or contentious forks.
PoS Core with PoW-like Rate Limiting adds lightweight puzzles to PoS as an anti-spam or MEV mitigation measure. If tuned poorly, the puzzle becomes either useless or wasteful, and governance can become contentious around difficulty control.
Hybrid designs are often chosen when fast finality and strong censorship-resistance assumptions are both required, or when a project wants PoS efficiency while actively counterbalancing stake-centralization pressures. However, hybrids multiply complexity risk, increase the auditing burden, and can create incentive misalignment when miners and stakers optimize for conflicting objectives. During crisis events, dual-authority governance can also degrade trust: if two subsystems disagree about the canonical chain, the community is forced back into social arbitration.
Proof of Stake Adoption in 2026
Proof of Stake adoption solidifies around established Layer 1 networks and expands aggressively into Layer 2 scaling solutions, driven by quantifiable participation growth and maturing validator economics. Ethereum's validator Annual Percentage Yield hovered near 3.15% in Q2 2025, anchoring expectations for continued network growth as validator economics matured and delegated staking became more competitive.
At the same time, scaling adoption tends to professionalize operations. Operator concentration, stake concentration, and custody concentration become the real decentralization battlegrounds. Where high throughput, ESG alignment, and fast finality matter—DeFi, gaming, enterprise chains—PoS is often an acceptable tradeoff. Where the dominant risk is censorship—uncensorable money, state-resistant publishing—PoW can still be the better default despite the energy overhead.
Proof of Work Use Cases in 2026
Proof of Work remains rational for three use-case templates:
- Sovereign digital stores of value like Bitcoin, where “physical anchoring” through externalized cost is a feature, not a bug, and predictable issuance supports long-term monetary policy credibility.
- Censorship-resistant publication and timestamping, where permissionless block production matters more than throughput, and the core threat model includes state-level adversaries.
- Fair-launch and equitable-distribution networks, where PoW is used to distribute coins from genesis without pre-mines or capital-gated validator entry.
PoW’s weaknesses (pool concentration, hardware supply chains, slower finality) remain real. But the objective, externalized attack-cost model and the ability for miners to redirect hashpower to different pools relatively quickly keeps PoW attractive in adversarial settings where neutrality is the priority.
Frequently Asked Questions
Which Is Better, Proof of Work or Proof of Stake?
No single consensus mechanism is universally "better"—the right choice depends entirely on your priorities and constraints. Proof of Work and Proof of Stake each excel in specific contexts, and understanding your goals helps clarify which mechanism aligns with your needs.
Is Ethereum Mined?
Ethereum operates exclusively on Proof of Stake consensus following The Merge, which finalized on September 15, 2022. This transition fundamentally altered how the network reaches agreement on the state of the blockchain, shifting from miners competing with computational power to validators staking capital. Furthermore, the term "Ethereum 2.0" has been deprecated by the community because it implied a separate chain; The Merge simply upgraded the existing Ethereum mainnet to use Proof of Stake consensus. The transition preserved all transaction history, balances, and smart contract state without requiring users to migrate funds or change addresses.
What are the Disadvantages of PoW and PoS?
Proof of Work's most misunderstood downside: The environmental impact isn't just about raw energy consumption—it's about where that energy comes from and the externalities imposed on local communities near large mining operations. The practical impact falls on electricity grids in regions with cheap power, sometimes straining infrastructure or displacing renewable energy that could serve residential needs, even when miners claim to use "stranded" or surplus energy.
Proof of Stake's most misunderstood downside: The "rich get richer" criticism oversimplifies wealth concentration—the real concern is that staking rewards accrue to those who can meet minimum thresholds or afford custodial services, potentially excluding smaller holders who can't meet validator requirements or don't trust delegation pools. The practical impact affects retail participants who must choose between accepting custodial risk (and fees) or forgoing staking rewards entirely, potentially widening the gap between institutional and individual participants over time.
In addition, both mechanisms face governance risks that are social rather than purely technical: Proof of Work mining pools can coordinate informally without violating protocol rules, and Proof of Stake validators can form cartels or face regulatory pressure to censor transactions, especially when staking concentrates in regulated custodial services.
What is Slashing in Staking?
Slashing is an economic penalty mechanism in Proof of Stake that destroys a portion of a validator's staked capital when they violate protocol rules, preventing malicious behavior without requiring external enforcement. The penalty aims to make attacks economically irrational by ensuring that rule-breakers lose more than they could gain from disrupting the network. Proof of Work does not have "slashing" because miners aren't staking capital—their economic penalty for invalid blocks is wasted electricity and opportunity cost (the energy could have mined a valid block on the honest chain).
Is Mining More Profitable than Staking?
Mining provides a more unreliable revenue stream than predictable yield in staking. The costs of mining are externalized in hardware, its maintenance, and energy; the upfront cost of staking is much cheaper but requires putting capital at risk of penalty for misbehaving, sometimes, outside of the staker’s control.




