How to Create a Cryptocurrency? A Beginner’s Guide

Key Takeaways
- 🆕 Your first decision is architectural: token vs coin. A token ships fast and inherits an existing chain’s security and tooling; a coin means owning consensus, networking, infrastructure, and long-term maintenance.
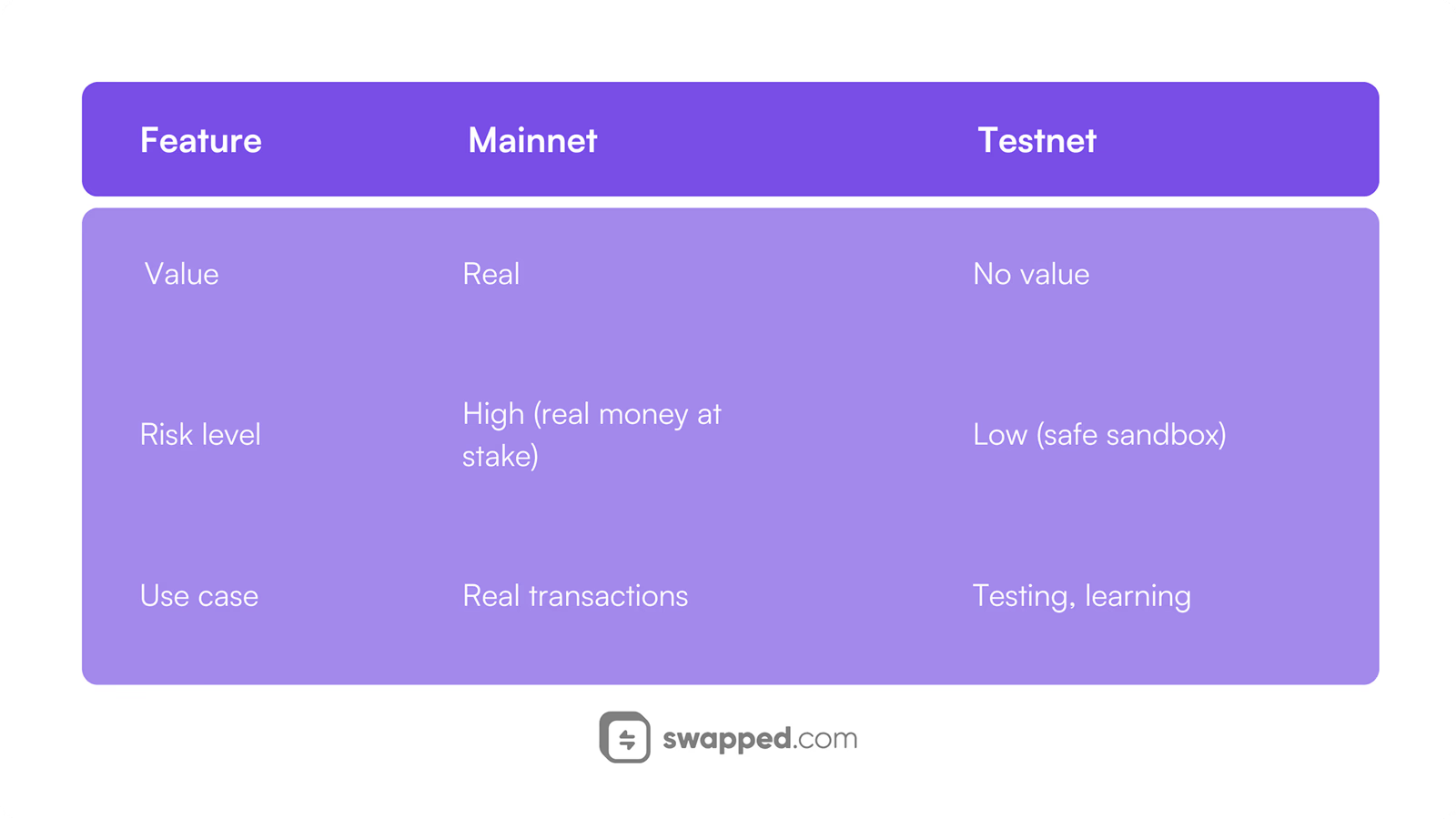
- 🆕 Don’t touch a testnet until your use case is specific: define target user, required on-chain actions, trust model (custodial vs non-custodial), and a measurable success metric (TVL, liquidity depth, DAU wallets, tx/day).
- 🆕 Pick a creation method that matches your skill tier and runway: no-code is for MVPs and memecoins; custom smart contracts are for production tokens; forking and new chains are infrastructure projects with ongoing security debt and ops burden. Treat budget like line items, not vibes: gas is the cheap part. Real costs come from audits, legal/compliance, liquidity provisioning, and recurring infrastructure + ops.
There are hundreds of thousands, if not millions, of coins and tokens on the crypto market today but for one reason or another, your project needs a brand new one. In this case, this guide is for you!
Creating a cryptocurrency in 2026 begins with one decision that sets the tone for everything that follows: are you deploying a token on an existing blockchain (fast, cost-effective, and powered by smart contracts), or are you launching a coin with its own blockchain (full sovereignty, but with real infrastructure and long-term maintenance)? The path you choose will shape your budget, your timeline, your technical workload, and, most importantly, whether your asset can actually create value beyond speculation.
By the end of this guide, you will have a concrete path forward, structured around the decisions that matter most in 2026.
Definitions and Background

Cryptocurrency creation starts with two distinct approaches: launching a native coin with its own blockchain protocol or deploying a programmable token on an existing network like Ethereum. A coin requires building and maintaining the underlying infrastructure: consensus rules, transaction validation, and network propagation. A token leverages smart contract functionality on established chains, operating within their existing security and fee structures.
Coins vs. Tokens
This distinction extends to the goals of a crypto asset. If your project requires fundamental control over consensus mechanics, transaction validation rules, and network-level parameters, then there is hardly a way around a coin with its own blockchain; if you're building an application-layer asset with specific functionality (governance, rewards, access rights), then a token on an existing chain is good enough for those requirements.
| Dimension | Coin (Native Asset) | Token (Contract Asset) |
|---|---|---|
| State Storage | Blockchain protocol maintains balances in native ledger | Smart contract on existing chain tracks ownership |
| Upgrade Mechanism | Protocol-level consensus changes require network-wide coordination | Contract upgrades via proxy patterns or redeployment |
| Transaction Fees | Paid in the coin itself (native gas) | Paid in the host chain's native coin (e.g., ETH for gas) |
Many people use "coin" colloquially to refer to any cryptocurrency, including tokens. However, throughout this guide, we’ll stick to the proper terminology: "coin" here on out strictly means a native asset with its own blockchain (Bitcoin, Ethereum's ETH, Solana's SOL), while "token" refers to assets created through smart contracts on existing networks (USDT on Ethereum, governance tokens on Polygon).
Protocol
Next, a protocol defines the mathematical and logical rules governing how a blockchain network reaches consensus, validates transactions, and transitions between states. It exists separately from implementation (the client software nodes run, like Bitcoin Core or Geth) and from smart contracts. Think of the protocol as the constitution, implementations as the interpreters of that constitution, and smart contracts as the laws passed under that framework.
The choice to develop a custom protocol is more applicable to projects that need to create a coin and blockchain for their own purposes. For token creation, studying and fully understanding the underlying network’s protocol is the requirement.
Protocols can exist without smart contract capability—Bitcoin operates as a UTXO-based protocol with limited scripting but no general-purpose contract execution—while smart contracts can exist without designing a new protocol, since tokens deploy onto chains like Ethereum where the protocol is already established and maintained.
Smart Contract
A smart contract is a deterministic program stored and executed on a blockchain. One implication of this technology is identical inputs always produce identical outputs regardless of which node processes the transaction, ensuring consensus across the network.
A contract address differs from a wallet address (derived from a public key, serves as a destination for funds): it points to executable code rather than a user-controlled key pair. Contracts don't have private keys, they have programmed logic defining when and how they release funds or modify state.
A simplified example of how a smart contract would work in an insurance environment. Source: Wikimedia Commons
Token contracts typically control these core functions:
- Minting: Creating new token units and assigning them to addresses (often restricted to contract owner or specific roles)
- Transfers: Moving tokens between addresses with balance verification and event logging
- Approvals and allowances: Granting third-party contracts or addresses permission to spend tokens on your behalf
- Burning: Permanently destroying tokens by sending them to inaccessible addresses or reducing total supply
- Roles and ownership: Access control determining which addresses can execute privileged functions
Smart contracts can be deployed as fully immutable (code cannot change after deployment) or upgradeable via proxy patterns (a proxy contract delegates calls to an implementation contract that can be swapped). Each approach carries distinct trust assumptions.
Token Standards
As the name implies, this is something only those who want to create a crypto token need to keep in mind, at least initially. A token standard defines a standardized interface (function signatures, events, and data structures) that wallets, exchanges, and decentralized applications rely on to interact with your token without custom integration for each project. Without adherence to recognized standards, your token becomes incompatible with existing infrastructure: exchanges can't list it, wallets can't display balances, and DeFi protocols can't integrate it.
Standards enable interoperability: when your token implements ERC-20, every Ethereum wallet automatically knows how to display your balance, every decentralized exchange can list trading pairs without custom code, and every analytics platform can track your token's movement across addresses. If your use case includes unique assets (like a non-fungible token collection), you’ll rely on different standards and indexing assumptions than fungible token deployments.
Initial Considerations
Before you touch a testnet or write a constructor, four decisions will decide whether you ship smoothly or end up rebuilding under pressure: use case clarity, technical skills, budget reality, and timeline discipline. Think of these as your guardrails—miss them, and your plan turns into expensive rework.
Use Case
Defining your use case requires more than deciding between "utility token" or "meme coin." You need to answer four specific questions that directly impact your architecture, your budget, and your timeline.
First, identify your target user: are you building for everyday consumers making payments, developers needing gas tokens for smart contracts, or enterprises requiring permissioned ledger access? A consumer-focused payment token demands different infrastructure than a developer-focused gas token.
Second, specify the on-chain actions your cryptocurrency must support. Will users only transfer tokens, or do you need staking mechanisms, governance voting, automated liquidity pool provisioning, or NFT minting capabilities? Each additional action increases complexity exponentially. If your use case requires staking, you're committing to tokenomics design decisions, consensus mechanism security, and mandatory audits on top of deployment.
Third, clarify your trust model: custodial or non-custodial? Custodial solutions (where you control user keys) simplify onboarding but introduce regulatory scrutiny and single-point-of-failure risks. Non-custodial approaches empower users but require robust wallet integration and key recovery mechanisms.
Fourth, define your success metric with precision. Is it daily active wallets, total value locked (TVL), transactions per day, or liquidity pool depth? Vague goals like "adoption" won't help you prioritize features. If your metric is TVL, you need mechanisms to attract and retain capital. If your metric is broader adoption, expect users to evaluate your token in the context of their broader crypto portfolio, which raises the bar on clarity, utility, and risk disclosures.
Technical Skills

Photo by Rohan on Unsplash
Non-technical founders can still launch cryptocurrencies using no-code platforms or template deployments, but you must be able to at least verify what you're deploying. At minimum, you need to read contract parameters (token name, symbol, decimals, total supply), verify the contract address on a block explorer, understand gas fee basics, and manage private key hygiene. If you can't perform these checks, you're outsourcing your entire security model to others, stacking up trust and risks.
Web developers comfortable with JavaScript and wallet integrations can handle token deployment with guidance, especially on chains like Ethereum or Binance Smart Chain where deployment tools are well-documented. You'll need to verify nonce management (transaction ordering), understand RPC endpoints (how your app communicates with the blockchain), and integrate wallet libraries (MetaMask, WalletConnect). This tier can deploy standard ERC-20 or BEP-20 tokens and customize basic parameters without writing smart contracts from scratch.
Smart contract developers proficient in Solidity or Rust come into the picture for custom token features: dynamic supply mechanisms, governance modules, staking rewards, or integration with DeFi protocols. This requires understanding gas optimization, security patterns (reentrancy guards, access controls), and audit preparation.
Building a custom blockchain requires the highest skills, which comes as no surprise. Protocol engineers with infrastructure experience can build or modify blockchain clients, consensus algorithms, and node infrastructure. This tier handles forks of Bitcoin, Ethereum, or Cosmos SDK chains, or builds entirely new blockchains.
Even with outsourced development, lacking any skills increases your timeline and budget because you can't verify deliverables or troubleshoot issues independently. You also need a dependency checklist of tools you'll interact with: a wallet (hot or hardware, like OneKey or Ledger), RPC endpoint access (Infura, Alchemy, or self-hosted nodes), block explorer familiarity (Etherscan, Solscan), testnet faucets for trial runs, and multisig wallet setup for team fund management.
Budget
Just like complexity, cryptocurrency creation costs vary wildly, so it helps to break the budget into line items you can actually control—and the hidden ones you cannot ignore.
Deployment and network fees are mandatory and vary by blockchain. For instance, deploying a token on Solana runs approximately 0.3 SOL plus minimal network fees (currently under $10 total), Ethereum or Layer 2 solutions cost around 0.01 ETH (fluctuating with gas fee prices, anywhere from $20 to $100), and Binance Smart Chain averages 0.19 BNB (roughly $115). These baseline deployment costs don't include audits, legal work, or liquidity.
Speaking of, audit and security review costs depend on smart contract complexity and the firm’s reputation. Even simple ERC-20 tokens might be audited for $5,000-$10,000, while complex DeFi protocols with staking, governance, and treasury management can exceed $50,000. Audits are mandatory if your contracts hold user funds or interact with other protocols; skipping them invites exploits but more importantly, destroys credibility.

Photo by Sasun Bughdaryan on Unsplash Sometimes, legal and compliance expenses arise if you're offering tokens to the public, especially in regulated jurisdictions. Token classification (security vs utility), registration requirements, and tax structuring require legal counsel; budget $10,000-$50,000 for comprehensive advice. If your distribution resembles an initial coin offering, your compliance budget and timeline should be treated as first-order constraints, not “optional later.”
Moving on from one-time expenses to ongoing costs, infrastructure spending—RPC node access, server hosting, dedicated validators—range from $100/month for third-party RPC services to $5,000+/month for self-hosted validator nodes on proof-of-stake chains. If your use case requires high transaction throughput or custom indexing, infrastructure becomes a significant recurring expense.
Liquidity provisioning is mandatory if you want tradable markets. Listing on decentralized exchanges (DEXs) requires you to seed liquidity pools—depending on target trading volume, it could be $50,000-$500,000. Centralized exchange listings add listing fees ($5,000-$1,000,000+) and market-making agreements.
Other ongoing operations—community management, security monitoring, protocol upgrades—cost $5,000 to $30,000 monthly for serious projects.
But wait, there is more! Some unexpected expenses can emerge: hidden costs from iteration of deployment versions, cost volatility from gas fees, and opportunity cost from delays. You can mitigate these by deploying on testnets first to validate logic before mainnet, timeboxing audit feedback cycles to avoid endless revisions, and staging liquidity provisioning to match traction rather than front-loading capital.
Timeline
If you consider the launch of a cryptocurrency a complete path, the process can take weeks to months. Even the contract deployment or client release are not a one-day affair.
Compiling token name, symbol, decimals, total supply, mint authority decisions (who can create more tokens), burn mechanism (deflationary or fixed supply), and initial distribution schedule requires completing discovery and specification. This can take a couple of weeks.
Next is implementation. Coding smart contracts, setting up infrastructure, and integrating wallet support until a functional prototype is deployed on testnet takes one to three months. For tokens, successful deployment criteria are basic transfer functionality, and role-based access controls validated. For new blockchains, it means nodes syncing, transactions confirming, and consensus functioning under test load. Testing for 3-8 weeks after that is best not to be skipped.
Before the launch, take 4-12 weeks and the budget for security review and audit. Only then it is generally considered acceptable to launch a cryptocurrency, and even then, verifying the contract on block explorer, seeding liquidity pools, and executing the initial distribution can take a week or two.
Cryptocurrency Creation Methods
There are about five distinct creation methods for launching a cryptocurrency, each with fundamentally different artifacts and engineering commitments. Three main architectural paths—deploying a token on an existing chain, forking an existing blockchain, or building a new blockchain from scratch—can be executed through different modes: no-code tools and blockchain-as-a-service platforms. Smart contract development, blockchain forking, and new blockchain development represent the core technical paths requiring direct engineering work.
No-Code Tools
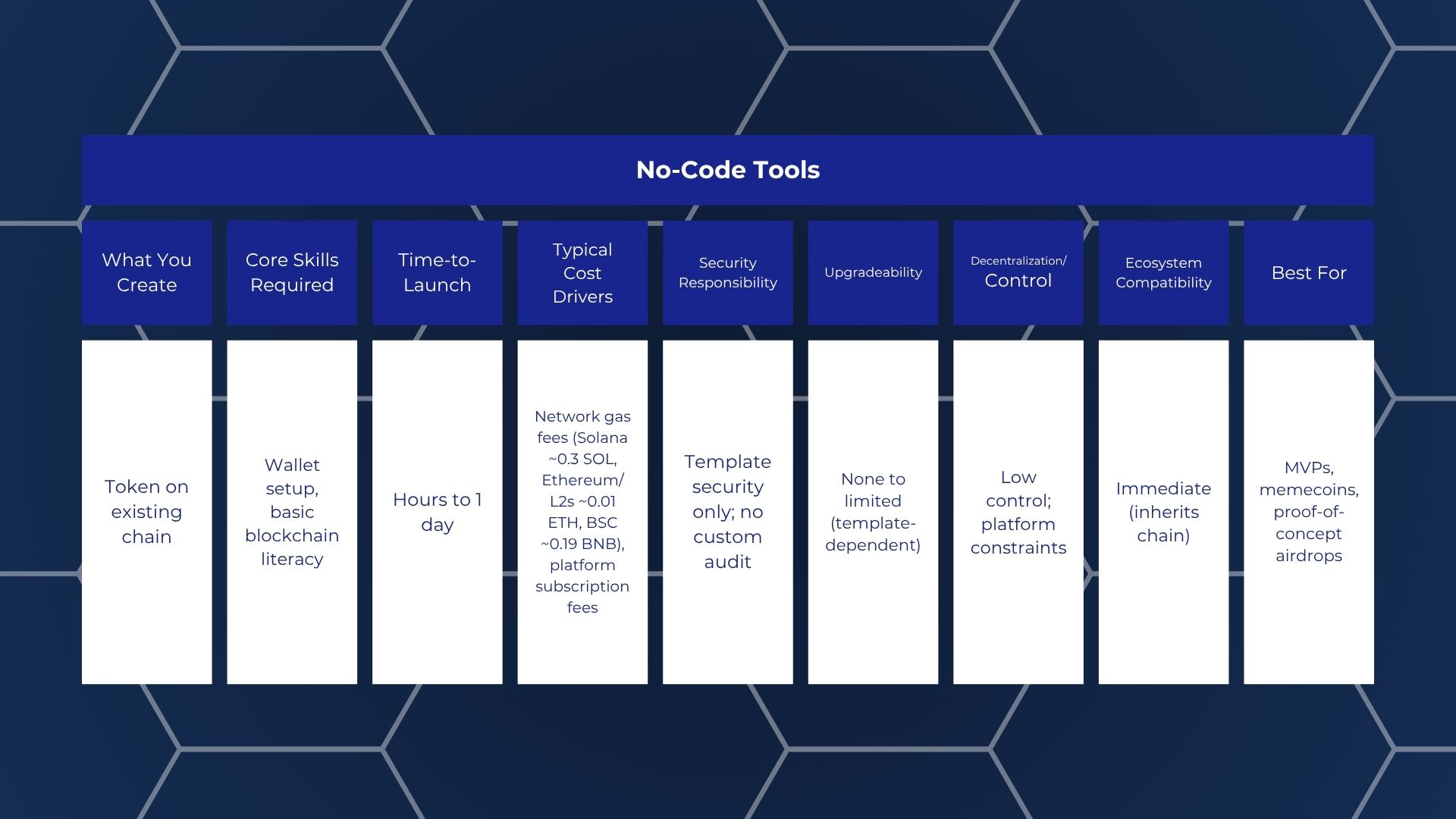
With those tools, you get a deployed ERC-20, BEP-20, or SPL token smart contract on a public blockchain, generated through a web interface without writing code. The token lives at a contract address on the chosen network and can be added to wallets immediately after deployment.
All you need is a compatible wallet (MetaMask, Phantom, Trust Wallet) funded with the native token of your chosen chain to cover gas fees. Basic understanding of token parameters like total supply and decimals is necessary, too, since these inputs directly affect the deployed contract.
- Most no-code generators offer fixed templates (standard ERC-20, mintable, burnable). Custom logic like vesting schedules, tiered fees, or conditional transfers is usually unavailable. If your use case requires non-standard behavior, you will outgrow the tool immediately after launch.
- Many templates assign contract ownership to the deploying wallet address without clearly explaining renunciation or transfer procedures. If you lose access to that wallet or fail to configure multi-signature control, upgradeability and administrative functions become permanently inaccessible.
- Token name, symbol, and decimals are typically immutable post-deployment in standard templates. Some platforms allow metadata updates through centralized registries, but these changes do not propagate automatically to all wallets and explorers, creating inconsistent user experiences.
- Automated contract verification on Etherscan, BscScan, or Solscan is not guaranteed. Unverified contracts display only bytecode, reducing trust and making it harder for exchanges or aggregators to list your token. Manual verification requires access to the exact compiler settings and source code, which some platforms do not expose.
- Transitioning from a no-code token to a custom contract later requires a token swap event—users must exchange old tokens for new ones. This process introduces friction, potential value loss during migration windows, and often requires smart contract escrow mechanisms that the original template cannot facilitate.
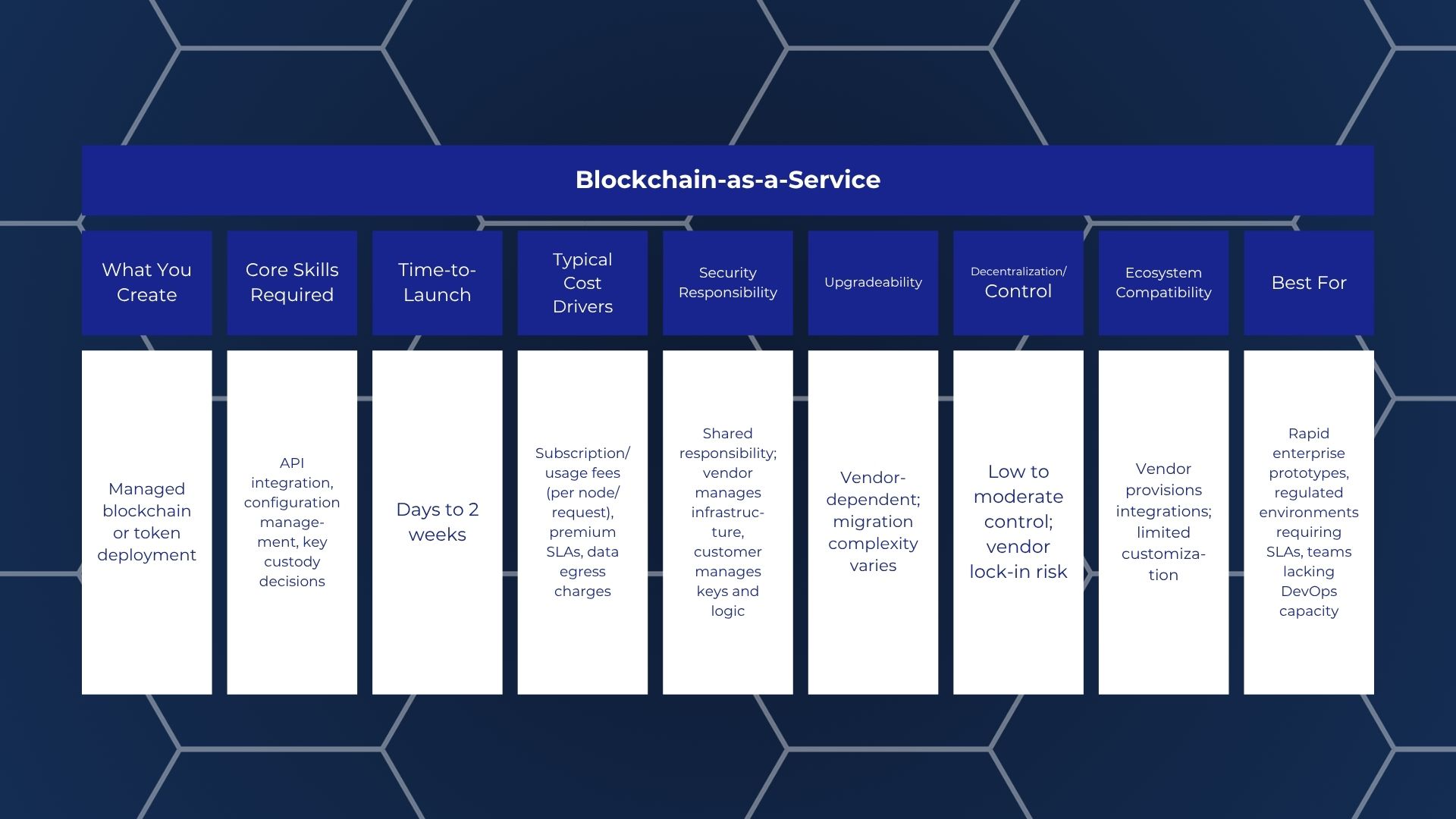
Smart Contract Development (Token on an Existing Chain)
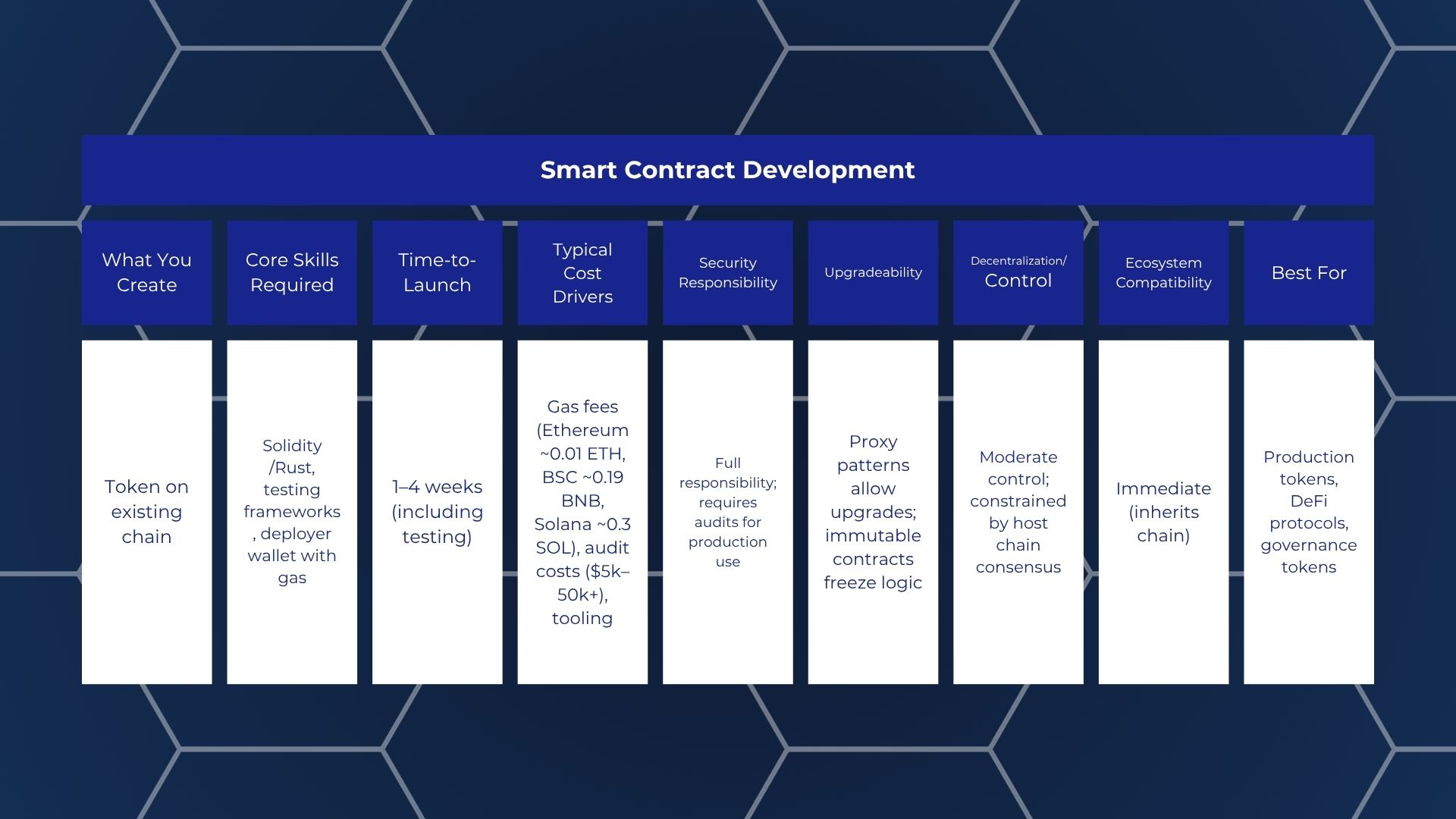
A custom smart contract deployed to an established blockchain (Ethereum, BSC, Polygon, Solana, Avalanche) gives you programmatic control over minting, burning, transfers, allowances, and any additional logic you code. The token inherits the host chain's security, consensus, and network effects but exists as an independent asset with its own contract address.
This method requires proficiency in the chain's smart contract language (Solidity for EVM chains, Rust for Solana). Plus, a local or cloud-based development environment with testing frameworks (Hardhat, Foundry, Anchor). A funded deployer wallet containing enough native tokens for gas fees or access to testnet faucets for pre-deployment testing is essential. For production launches, budget for third-party audits and node RPC access if you cannot rely solely on public endpoints.
- Decide whether your contract retains a mint function and who controls it. Retaining mintable authority allows future supply adjustments but introduces centralization risk; renouncing ownership by transferring control to the zero address makes the contract immutable and trustless but eliminates all administrative capabilities, including pausing or upgrading. This decision is irreversible in non-upgradeable contracts.
- Implementing pause functionality allows you to halt all transfers during emergencies but centralizes control in the pause authority's hands. Blacklisting specific addresses enables regulatory compliance or fraud response but contradicts decentralization principles. Both features require explicit governance structures to prevent abuse and must be disclosed transparently to users and auditors.
- Proxy patterns (Transparent, UUPS) separate logic from state, allowing you to upgrade contract behavior without changing the token's address or requiring user migration. However, upgradeable contracts introduce complexity, higher gas costs, and storage collision risks. Immutable contracts are simpler and more trustworthy but cannot fix bugs or adapt to protocol changes once deployed.
- Implementing EIP-2612 permit functionality allows users to approve token spending via off-chain signatures instead of on-chain transactions, improving user experience by eliminating the two-step approve-then-transfer flow. However, permit adds code complexity and requires careful nonce management to prevent replay attacks.
- The decimals value (typically 18 for ERC-20 compatibility) and initial total supply are set in the constructor and cannot be changed post-deployment in most standard implementations. Choosing 18 decimals ensures compatibility with DeFi protocols and wallets expecting wei-denominated values, while lower decimals (e.g., 6 for stablecoin parity with USDC) simplify human readability but may cause rounding errors in complex calculations.
Blockchain Forking
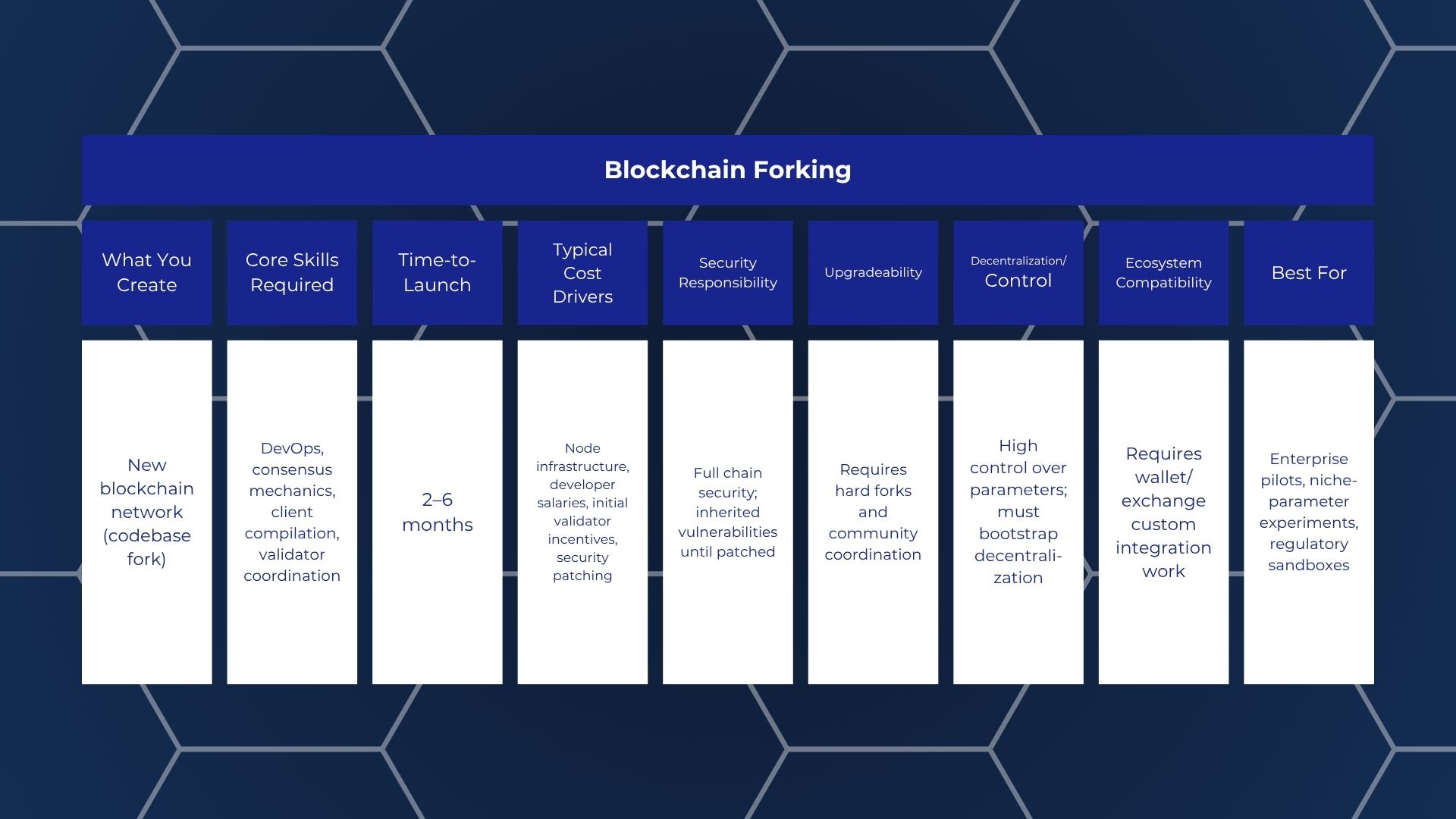
Even complex setups may work without creating a blockchain protocol from scratch, with a new blockchain network derived from an existing codebase instead. "Forking" in this context refers to a codebase fork that creates a new independent network, not a chain-state fork like Bitcoin Cash or Ethereum Classic. Your fork, therefore, produces its own native coin, genesis block, and independent transaction history.
It might sound simple but still needs deep familiarity with the source blockchain's architecture, including client software internals, P2P networking protocols, and consensus implementation.
- Change the chain ID (EIP-155 for EVM chains) to prevent transaction replay attacks between your fork and the original chain. Failure to update this identifier allows malicious actors to replay transactions across both networks, draining user funds.
- The genesis block defines initial state, including pre-mined balances, timestamp, difficulty, and configuration parameters. Distribute initial coin supply to founding wallets, adjust block time targets, set initial gas limits, and configure consensus parameters.
- Hardcode seed node addresses into the client software to enable peer discovery. Without trusted bootstrap nodes, new participants cannot join your network. Initial validators must be coordinated off-chain via governance calls or foundation agreements, as no decentralized mechanism exists at genesis.
- Modifying existing parameters (block reward, gas limit, block interval) requires minimal code changes but still demands rigorous testing to avoid unintended economic or security consequences.
- The parent codebase as a rule receives regular updates fixing vulnerabilities, optimizing performance, and adding features. You must monitor upstream development, selectively backport patches to your fork, and test compatibility with your modifications.
New Blockchain Development
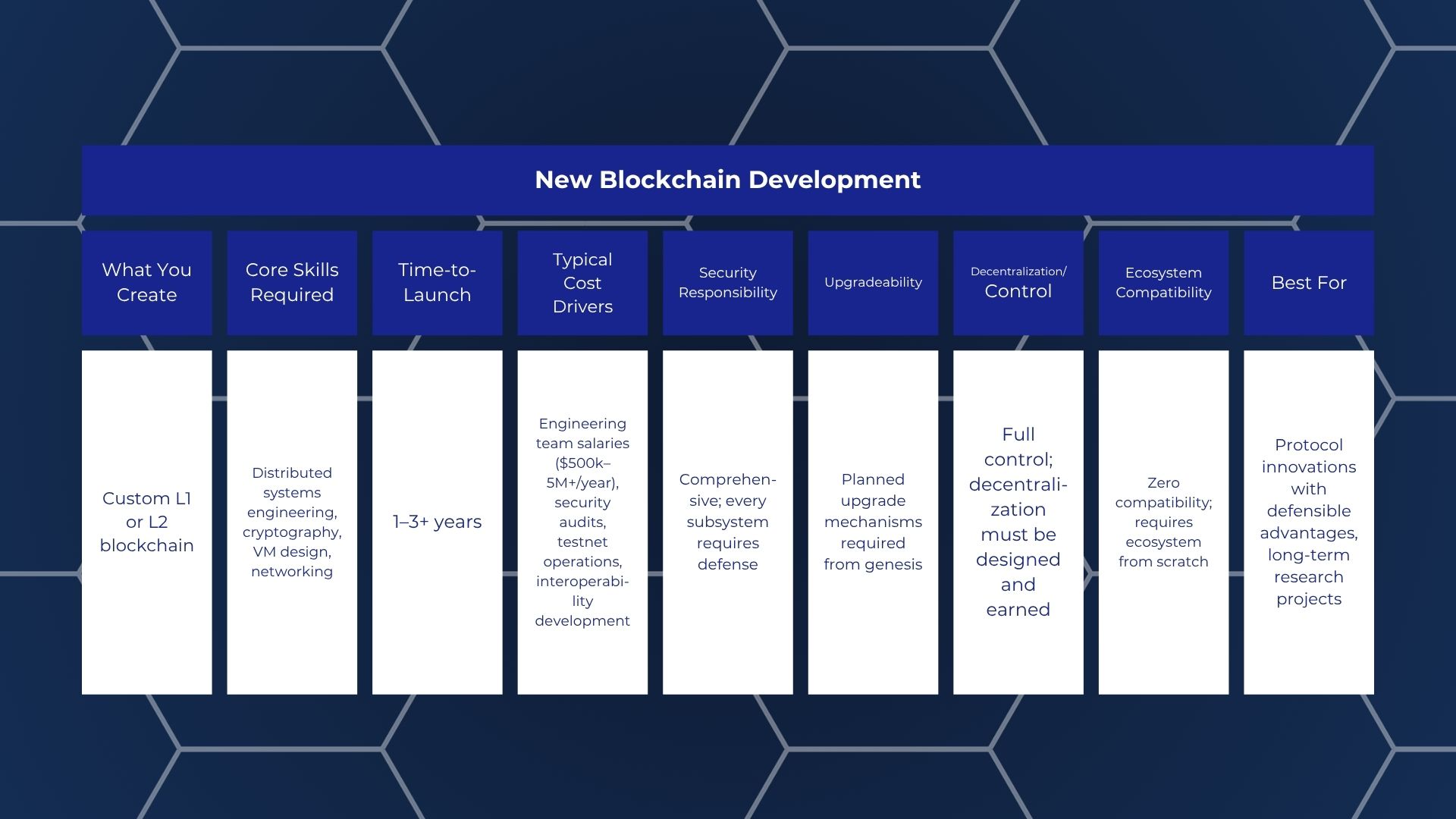
Last but not least, your needs may call for a purpose-built L1 blockchain or L2 scaling solution designed from architectural first principles, with custom consensus, state model, virtual machine, and economic mechanisms. This path produces a sovereign network that does not inherit technical debt, design constraints, or governance structures from existing chains.
Components to plan include but are not limited to consensus and validator economics, networking and peer-to-peer layer, mempool and transaction ordering, state model and virtual machine, fee market and economic sustainability, RPC and indexing infrastructure, block explorer integration, and so on.
Token and Network Design
The previous section was only about network choice. Next, token and network design determines whether your cryptocurrency project survives its first month or collapses under preventable economics, governance conflicts, or infrastructure mismatches.
Tokenomics
Coin or token’s economic design requires forcing coherence across every parameter you publish. Before selecting supply caps or emission schedules, create a tokenomics design checklist that prevents contradictions between your objectives and constraints.
This checklist must include: (1) the objective function defining which behaviors you incentivize (long-term holding, liquidity provision, governance participation, protocol usage), (2) constraints you face (regulatory compliance boundaries, user experience limitations, budget caps, security assumptions), and (3) the parameter set you will publish: total supply, decimals, transaction fees, emission schedules, vesting terms, treasury allocation, governance scope.
Misalignment between your objective function and parameter set creates exploitable gaps, so consider all aspects simultaneously. For example, if your goal is long-term ecosystem growth but your vesting schedules release 40% of tokens in month one, early holders dump and new users face inflated entry prices.
Supply Model
Supply model parameters define the total economic space your token occupies and how that space expands or contracts over time. It consists of a few parameters, defining each is necessary to create a complete and viable supply model.
| Parameter | Specification | Governance Method |
|---|---|---|
| Total Supply | Fixed cap (e.g., 21M) or uncapped with rate limits | Immutable in contract or DAO proposal required |
| Initial Circulating Supply | Tokens available at launch (e.g., 15% of total) | Set in deployment, locked by vesting contracts |
| Emission Rate Schedule | Linear release (e.g., 5% per year) or halving events | Defined in contract logic or adjustable via governance |
| Inflation Target | Annual percentage (e.g., 2% perpetual inflation) | Fixed algorithmically or votable parameter |
| Mint Authority | Contract admin, DAO treasury, or none | Renounced, timelock-controlled, or multisig |
| Burn Mechanism | Fee burns, protocol buybacks, manual burns | Automatic in transaction logic or governance-triggered |
Moreover, emission schedules interact with user behavior. Rapid early emissions can bootstrap liquidity but result in a risk of dumping pressure; vice versa, slow emissions protect price stability but delay ecosystem incentives. Step functions (releasing large tranches at intervals) create predictable sell walls unless paired with utility demand that absorbs new supply.
Distribution Model
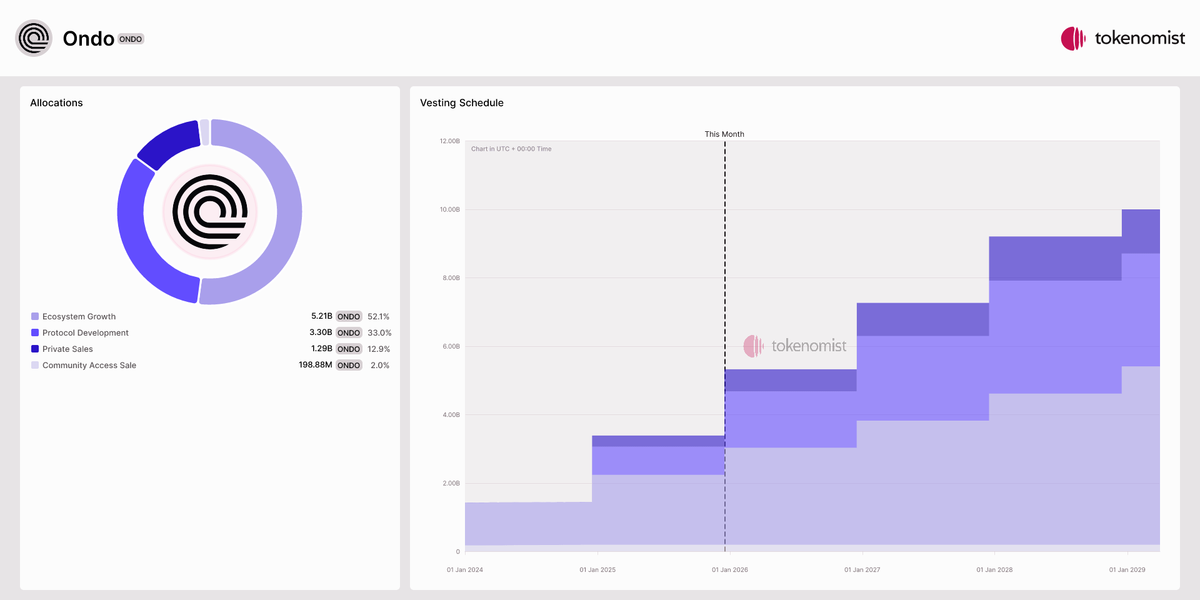
ONDO token distribution and release schedule as an example. Source: tokenomist.ai
Distribution model design determines who gets and holds tokens at launch, how they receive them, and when locked tokens enter circulation. The distribution primitives are similarly concrete: airdrop criteria design (snapshot dates, eligibility rules), team and investor vesting cliffs and linear vesting, liquidity provisioning allocation (percentage reserved for DEX pools), ecosystem and treasury allocation (grants, partnerships, future development), and anti-collusion considerations for early distribution (wallet age requirements, transaction history minimums, Gitcoin Passport scores).
Vesting prevents immediate dumps and aligns long-term incentives. Standard team vesting uses a 12-month cliff followed by 36-month linear vesting. Investor vesting often has shorter cliffs but similar linear schedules. Liquidity allocations typically unlock immediately to enable trading, but teams should pair this with liquidity lock commitments (12-24 months) to prevent rug pulls.
Treasury allocations commonly found in most high-profile launches fund ongoing development but require governance controls to prevent insider enrichment. Specify spending limits per proposal, require multisig approvals for large transfers, and publish quarterly treasury reports showing inflows, outflows, and remaining balances.
Utility Model
This is not the same as coming up with a use case; utility design forces a distinction between token required for protocol function, token used for incentives, token as fee or discount, and token for access or rights by defining how your token or coin captures value from the platform’s or project’s usage.
| User Action | On-Chain Token Interaction | Why This Creates Sustainable Demand |
|---|---|---|
| Staking for yield | Lock tokens in staking contract | Reduces circulating supply; users pay opportunity cost for rewards |
| Governance voting | Delegate or lock tokens to vote | Active participation requires holding; higher voting power incentivizes accumulation |
| Protocol fee payment | Burn or transfer tokens per transaction | Every transaction creates buy pressure or removes supply permanently |
| Liquidity provision | Deposit token pairs into AMM pool | Requires continuous token holding; fees reward long-term provision |
| Membership access | Hold minimum balance for premium features | Creates price floor; users must maintain holdings to retain access |
Avoid circular utility where tokens are only used to earn more tokens without external value creation. Sustainable utility connects token interactions to real economic activity.
Governance Model
Since you are here, your coin- or token-to-be will be governed in a decentralized manner, which comes with challenges that need to be considered in your cryptocurrency’s design. The governance model does not materialize from nothing but is composed of parameters that define governance scope, quorum and thresholds, voting power calculation, timelocks, emergency pause roles, and upgrade path.
Standard configurations balance accessibility with security. Timelocks give users time to exit before harmful proposals execute but slow response to urgent issues.
Delegated voting solves low participation without sacrificing decentralization. Quadratic voting reduces plutocracy but introduces complexity and collusion risks; use it only if sybil resistance is strong and community culture supports cooperation.
Emergency pause roles protect against exploits but centralize risk. Mitigate this with transparent multisig membership, high signature thresholds, rotation schedules, and timelocks on pause role changes.
Governance attack surfaces are varied but have well-known mitigation tactics:
- Vote buying → Mitigation: timelocks; lock voting tokens for the timelock period
- Low participation → Mitigation: delegated voting; progressive quorum reduction
- Treasury-drain proposals → Mitigation: spending caps; multisig co-sign; public review
- Parameter capture → Mitigation: caps per proposal; supermajority for economic changes
Branding

And how can we forget the niceties? Token branding extends beyond logos and names into execution-critical identity specifications that affect exchange listings, wallet integrations, and block explorer displays.
Before deploying contracts, complete these branding decisions: search CoinGecko, CoinMarketCap, and major exchanges to ensure your proposed ticker is not already used by another project. Coordinate the choice of decimal display with your utility model requirements. Keep the token name short, while avoiding special characters that break APIs, and make the purpose clear while you are at it.
Prepare PNG and SVG logo files well in advance and submit to relevant repositories and listing forms. Prepare a website, social links, description, and tags in advance for consistent submissions and metadata for explorers and wallets.
Step-by-Step Process to Launch a Cryptocurrency in 2026
Launch, in the context of this runbook, means successfully deploying your cryptocurrency or token to a live production environment, verifying its contracts, executing initial distribution according to your tokenomics, establishing initial liquidity, and making it available on at least one trading venue.
Note: This section will assume you have already completed the design phase—to recap, token economics, network architecture, and consensus mechanisms are documented—and that legal and compliance frameworks are being handled through appropriate channels.
Objectives and Requirements
What are you building and why? Be brutally honest. The objective-setting phase forces you to articulate not just your vision but the practical constraints that will shape every subsequent decision. Without this clarity, you risk building on sand; elegant architecture that doesn't match market reality or regulatory boundaries.
Goals:
- Establish measurable success criteria for the launch
- Document all technical, operational, and market-facing requirements
- Align team roles and responsibilities with launch milestones
Go/No-Go Checks:
- Can you articulate the launch in one sentence that includes asset type, target chain, and primary use case?
- Do you have documented answers to all items in the requirements checklist?
- Has at least one external stakeholder (advisor, potential partner, or pilot user) reviewed and validated your objectives?
Architecture and Chain
Architecture selection at this step determines nearly everything downstream: gas costs, developer tooling, security trade-offs, and user experience.
We have covered no-code tools vs. token via smart contract vs. dedicated blockchain but what about L2 vs L1? Choose Layer 2 over Layer 1 when you need the main chain's security guarantees but lower transaction costs and higher throughput. Consequently, Layer 1 is for when you require full sovereignty, custom consensus, or when your use case doesn't align with the main chain's roadmap.
Deployment costs vary dramatically by architecture. Token creation on Ethereum mainnet might cost $50-500 in gas fees depending on network congestion. Forking a chain adds ongoing infrastructure costs, and creating a new blockchain from scratch requires substantial development costs before ongoing operations.
Go/No-Go Checks:
- Does your chosen architecture support your minimum required transaction throughput?
- Can your budget accommodate deployment plus 6 months of infrastructure costs?
- Are at least two qualified developers on your team familiar with the chosen chain/language/tooling?
Development and Wallet Tooling
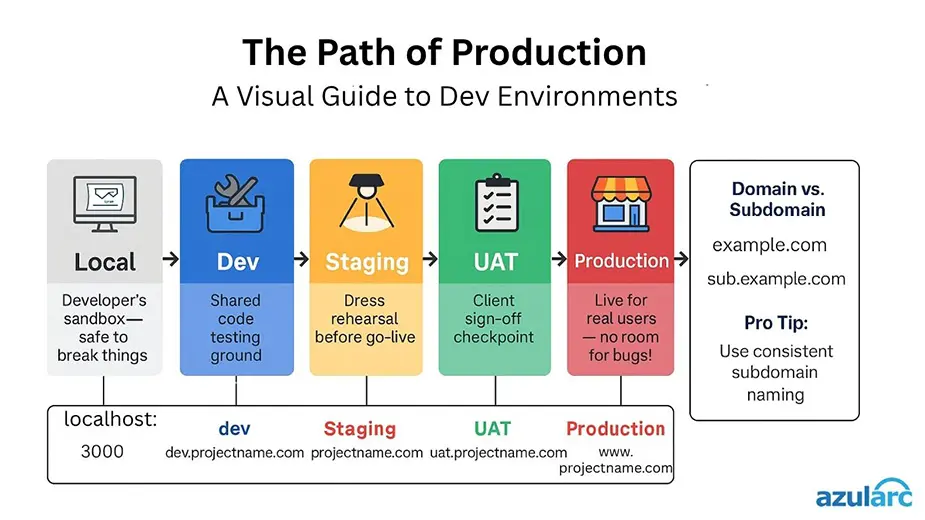
Source: Azul Arc
Development infrastructure is where mistakes compound silently. Inadequate tooling or sloppy environment separation causes the majority of launch delays and post-launch incidents. This step establishes the baseline hygiene that prevents you from accidentally deploying to mainnet with test keys or losing treasury funds because you didn't rehearse multisig workflows.
Maintain three distinct environments—development (local or private testnet), testing (public testnet matching your target chain), and production (mainnet). Each environment must use separate wallets, separate RPC endpoints, and separate deployment scripts with environment variables clearly labeled. Mixing environments is the #1 cause of accidental mainnet deployments with test code.
Define at minimum the following key roles:
- Deployer: Wallet that executes initial contract deployment (may be discarded or transferred post-launch)
- Admin/Owner: Wallet(s) with privileged contract functions (pause, upgrade, mint, parameter changes)
- Treasury: Wallet(s) holding undistributed token supply or protocol revenue
Private keys to relevant addresses can be stored in a hardware wallet, multisig hot or cold wallet. For most launches, Admin and Treasury roles should use multisig, while Deployer can be a hardware wallet-secured EOA.
By the way, before going to testnet, you have the option to rehearse the entire deployment on a local fork or simulation. Capture every transaction, verify gas estimates, confirm contract interactions work as expected.
Go/No-Go Checks:
- Have you successfully deployed and interacted with your contracts on a local fork?
- Do all team members with key roles have hardware wallets or secure key storage?
- Is your multisig configuration documented with recovery procedures if a signer is unavailable?
Smart Contracts or Core Protocol Implementation
This step is where design meets reality. Whether you're writing Solidity for Ethereum, Move for SUI Network, or Rust for a custom chain, the code you deploy will often be immutable (or difficult to change), so every line must be deliberate. This phase requires not just coding but systematic enumeration of what you're building and what you're explicitly leaving out.
Goals:
- Deliver production-ready smart contracts or protocol code
- Document every module's scope and known limitations
- Eliminate common access-control vulnerabilities before audit
Contract Surface Area Inventory: Before you write a single line of code, enumerate every contract module and explicitly mark it in-scope or out-of-scope for your launch:
- Token Contract: Core asset (ERC-20, SPL, or custom standard)
- Vesting Contract: Time-locked distribution for team/advisors
- Airdrop/Claim Contract: Merkle tree or allowlist-based distribution
- Treasury Contract: Protocol-owned funds management
- Governance Contract: Voting or proposal mechanisms
- Upgradeability/Proxy: Ability to change contract logic post-deployment
- Access Control: Who can call privileged functions (mint, burn, pause, upgrade)
For each in-scope module, document the business logic, privileged roles, and any assumptions.
Go/No-Go Checks:
- Does every privileged function have a documented business justification and access policy?
- Have you explicitly reviewed and accepted the risks of any in-scope upgradeability mechanisms?
- Can a new developer on your team understand the contract architecture from the documentation alone?
Testnet Deployment and Testing
Source: Swapped.com
Here comes your dress rehearsal. Testing is your last chance to catch integration bugs, gas estimation errors, and workflow missteps in an environment that mirrors mainnet without financial consequences. Skipping this phase or rushing through it is the surest way to deploy broken code to production and end up “rekting” your users.
Your test plan must cover: Unit Tests; Integration Tests; Fork Tests; Invariant/Property Tests; and Adversarial Tests. Run this full suite on testnet after deployment, and treat testnet as hostile.
Execute the exact sequence you'll use on mainnet, in order, and record every transaction hash:
- Deploy contracts
- Verify source code on block explorer
- Execute initial token distribution (to placeholder addresses)
- Add liquidity to a testnet DEX
- Confirm token is tradable
Go/No-Go Checks:
- Have you completed at least 100 transactions on testnet without unexpected failures?
- Did external testers or community members successfully interact with your testnet contracts?
- Are all critical and high-severity bugs from testnet resolved before mainnet?
Security Review and Audit Prep
Security in crypto is always non-negotiable. Even if you plan to launch without a formal audit, you must conduct an internal security review and prepare an audit-readiness packet.
If you're engaging auditors (or conducting internal review), provide architecture diagrams, threat model, testnet contract addresses, deployment scripts, privileged roles documentation, known issues and accepted risks. Establish a code freeze deadline. After this cutoff, no changes are permitted except via a documented hotfix process. Plus:
- Have at least two experienced developers conducted line-by-line code review?
- Are all critical and high-severity findings from internal review resolved?
- Is the audit-readiness packet complete enough that an external auditor could begin work immediately?
Mainnet Deployment
Finally, this is the moment everything becomes virtually irreversible. Once contracts are on-chain, they're permanent (unless you built in upgradeability, which carries its own risks). This step demands precision, checklists, and a clear abort criterion. Rushing here costs money and reputation.
- Deploy production contracts to mainnet without errors
- Capture an immutable launch record for future reference
- Execute role transfers, timelocks, and post-deployment configuration
What Next?
Although we have provided step-by-step instructions to creating your own cryptocurrency only up to the moment of mainnet deployment, keep in mind that it does not stop here. Securing the code and dependencies, while alleviating legal risks, and promoting the project all at the same time are no less deserving of a dedicated guide.
Where can you get the complimentary information on the ongoing management of a cryptocurrency? Try our other guides: one about wallet security best practices, another on commodity vs security when it comes to legally defining crypto assets, and a guide on how to create a meme coin for good measure.
Frequently Asked Questions
How much does it cost to create a cryptocurrency?
Creating a token on an existing blockchain can cost anywhere from under $1 to tens of thousands of dollars, depending on your project's complexity and compliance requirements. The three main methods — creating a new blockchain, altering or forking an existing blockchain, or generating a token on an existing blockchain — drive very different cost structures, with on-chain token generation being the most accessible starting point.
- Cheap (under $1,000): No-code token generator, testnet-only deployment, no audit, no legal review, minimal liquidity. Suitable for education or internal experiments, not public launches.
- Serious ($5,000–$50,000): Custom token, manual audit, basic legal consultation, initial DEX liquidity, verified contracts, testnet soak testing. Covers most community-driven or utility token projects.
- Full-scale ($100,000+): Advanced tokenomics, multi-chain strategy, comprehensive audit + ongoing monitoring, securities/jurisdiction structuring, tier-1 exchange listings, enterprise infrastructure, professional marketing.
Is it legal to create a cryptocurrency?
Creating a cryptocurrency token itself is generally legal in most jurisdictions, but distributing, marketing, or selling it may trigger securities laws, anti-money laundering rules, and tax obligations that vary by country. The legality depends less on the act of writing smart contract code and more on how you position, sell, and operate the token.
How do I choose the token supply size?
Choose your total supply size based on target unit price psychology, decimal precision, distribution plan, emissions schedule, and vesting structure, keeping in mind that supply alone does not determine market cap.
Can I launch a multi-chain token?
Yes, you can launch a token across multiple blockchains either by deploying native contracts on each chain or by using bridges to create wrapped representations, but each approach has distinct security, UX, and operational tradeoffs. Not to mention, the economic model has to account for the reality of siloed networks even when bridges are a factor.
Are no-code tools viable for serious crypto projects?
No-code token generators are viable for simple, short-term experiments or educational purposes, but serious projects with custom tokenomics, upgradeability needs, or long-term ambitions should hire developers or audit firms to avoid locked-in limitations and migration headaches. Viability depends on how much control, flexibility, and security your project requires.