What is the Meaning of FUD in Crypto? The Complete Guide

Key Takeaways
- 🤥 FUD = Fear, Uncertainty, Doubt — a communication tactic that manipulates decisions by amplifying negative perception without leaning on verifiable proof. Fear / Uncertainty / Doubt stack on purpose: fear creates urgency, uncertainty blocks verification, doubt erodes trust—enough to push people into panic, paralysis, or abandonment.
- 🤥 Not every negative claim is FUD. Use the three filters: verifiability (can you check it?), intent (inform vs. manipulate?), and proportionality (does the framing match the risk?).
- 🤥 In fast-moving arenas (especially crypto), rumors can become self-fulfilling via amplification → volatility → forced reactions (liquidations, spread widening, de-risking) before facts catch up.
- 🤥 The practical defense is a repeatable workflow: extract 1–3 testable claims, find primary sources, cross-check independent validators, and label the result True / False / Misleading / Unverifiable—then stop feeding the algorithm by not amplifying what you’re verifying.
At its core, FUD is manufactured uncertainty and in many cases, a form of disinformation, designed to blur the line between legitimate concern and propaganda. Today, when fact-checking struggles to keep pace with viral content, distinguishing between warranted caution and deliberate manipulation is an essential skill for anyone managing assets, reputation, or strategic communications.
FUD Definition and Origin
FUD is a tactic that deliberately spreads fear, uncertainty, and doubt to manipulate decision-making and behavior, typically employed as a competitive weapon in marketing, politics, and investment contexts. Instead of relying on verifiable claims or evidence-based arguments, FUD leans on emotional triggers and information gaps to steer audiences away from a choice.
The crypto world is an almost entirely online phenomenon that only recently has started making an impact on the real world, not the other way around. And since information also thrives online, whether legitimate or not, the two have a very close relationship. The point is, FUD is a concept all too familiar in the crypto circles, so knowing how to handle it is a survival skill.
Definition
First things first: FUD stands for “fear, uncertainty, doubt”. FUD is best understood as strategic communication that intentionally amplifies negative perceptions without necessarily providing substantiated proof.
Three boundary conditions usually separate it from other forms of negative messaging: Firstly, FUD is typically intentional rather than accidental misinformation. The spreader chooses to emphasize worst-case scenarios or exaggerate risks, knowing these claims lack full verification. Secondly, FUD aims to influence decisions—it’s not passive commentary but active persuasion designed to trigger delay, switching behavior, or abandonment. Thirdly, and most importantly, FUD relies on uncertainty rather than verifiable claims. Evidence-based criticism gives you data points you can test but FUD thrives in gray zones, where proof is hard to obtain quickly.
That’s why FUD is not the same as legitimate “fear appeals” used in public health campaigns or safety warnings, which rely on documented risks and aim to protect rather than manipulate. It also differs from ordinary risk disclosures that you see in financial prospectuses or product warnings which transparently lists known hazards instead of manufacturing perceived threats for competitive advantage.
Meaning
Mechanically, FUD targets the decision outcome by introducing cognitive friction at the moment of choice. It aims to make audiences delay adoption, switch to alternative vendors or solutions, avoid entering new markets entirely, or exit positions prematurely; in investment settings in particular, panic selling can directly benefit the spreader. From a behavioral psychology standpoint, FUD works by increasing perceived downside while reducing perceived ability to verify, nudging people toward avoidance.
There’s also a practical distinction you’ll see everywhere online: FUD as a tactic is the deliberate deployment by competitors, critics, or threatened incumbents (the “verb” form—“to FUD someone”). Opposite to that is FUD as a market sentiment label is the atmosphere created when the tactic saturates a space (the “noun” form—“there’s a lot of FUD around”).
This matters in cryptocurrency and investing communities, where calling something “just FUD” can become a reflexive defense against legitimate criticism. If you want peace of mind, you need to judge the evidence, not the vibe.
Etymology and Origin
The Fear / Uncertainty / Doubt triad is canonically used across marketing, technology, and investment contexts:
- Fear is the emotional accelerant, triggering threat responses that short-circuit rational analysis.
- Uncertainty creates information gaps that block confident decision-making.
- Doubt undermines trust in your sources—or even your previous decisions.
Uncertainty and doubt multiply fear. A fearful person with complete information can still act decisively but add uncertainty about outcomes or doubt about reliability, and paralysis kicks in. That decision-blocking anxiety is exactly what FUD spreaders want.
The historical emergence of “FUD” as terminology follows a clear trajectory. The term circulated in business and political contexts from the 1920s, but the abbreviated form became widely popular in the 1970s as a marketing label for competitive tactics. Gene Amdahl used “FUD” in 1975 to describe IBM’s competitive messaging strategy: leveraging uncertainty about competitors’ roadmaps to maintain dominance in mainframes. The concept has moved from propaganda techniques into standard vocabulary across technology, finance, and political discourse.
By Paul Downey on Flickr, 2007. Source: Wikimedia Commons
Information technology was especially vulnerable because evaluation requires expertise many buyers don’t have. That vulnerability—complex decisions made under incomplete information—is the same reason FUD later became so prominent in investing communities and, in particular, crypto.
Common Misuses of FUD
Despite the usage you might see in the wild, not every uncomfortable claim is FUD. These are often mislabeled:
- Legitimate criticism backed by evidence: Documented security vulnerabilities, failed promises, or regulatory violations aren’t FUD if they can be independently verified.
- Evidence-based risk warnings: Analysts explaining why valuations look unsustainable, or researchers disclosing actual flaws, are providing caution, not manufactured doubt.
- Bad news reporting: Journalists covering exchange hacks, regulatory actions, or project failures are doing transparency work, even if the news inevitably leads to anxiety.
The real test comes down to verifiability (can it be checked?), intent (inform or manipulate?), and proportionality (does the framing match the actual risk?).
Spotting the Three Components of FUD
These elements stack by design: fear creates urgency, uncertainty removes confidence in facts, and doubt chips away at trust—often enough to make people act before they can verify.
Fear
This messaging amplifies threat perception to trigger an emotional response instead of an analytical one. Common patterns include:
- Catastrophic framing: Worst-case scenarios presented as inevitable (“This change will destroy all value”)
- Imminent threat claims: Artificial urgency with unsubstantiated deadlines (“You have 48 hours before it’s too late”)
- Safety risk insinuations: Suggesting financial, physical, or reputational harm without concrete evidence
In cryptocurrency, fear often targets security (“wallet exploit imminent”), regulation (“government shutdown coming”), or existential project risks (“team abandoning development”). The telltale sign is straightforward: the message demands action before verification becomes possible.
Uncertainty
Uncertainty isn’t the same as “we don’t know yet” but deliberate obscuring that blocks decision-making.
Common tactics:
- Selective ambiguity: Removing context from true statements so they look unclear and suspicious
- Question flooding: Dozens of unverifiable concerns that create cognitive overload
- Anonymous authority citations: “Insiders confirm” or “experts are questioning” without attribution
Can the claim be verified through primary sources (blockchain data, official announcements, regulatory filings)? Does it offer specific evidence—or only vague implications? Manufactured uncertainty exploits the human tendency to want complete information. When someone floods you with unanswerable questions, you can end up frozen even when there’s enough data to act rationally.
Doubt
The third and final component is about confidence erosion: undermining trust without supplying real counter-evidence.
Common tactics:
- Insinuation without evidence: Rhetorical questions that imply wrongdoing (“Why won’t they address these concerns?”)
- Cherry-picked edge cases: Rare exceptions inflated into “the norm”
- Credibility attacks: Attacking messengers instead of addressing substance
In crypto markets, doubt campaigns frequently target team legitimacy, credentials, or technology viability. You’ll see small inconsistencies amplified while substantial evidence of progress or security is ignored—because the goal is discomfort, not clarity.
FUD in Cryptocurrency Markets
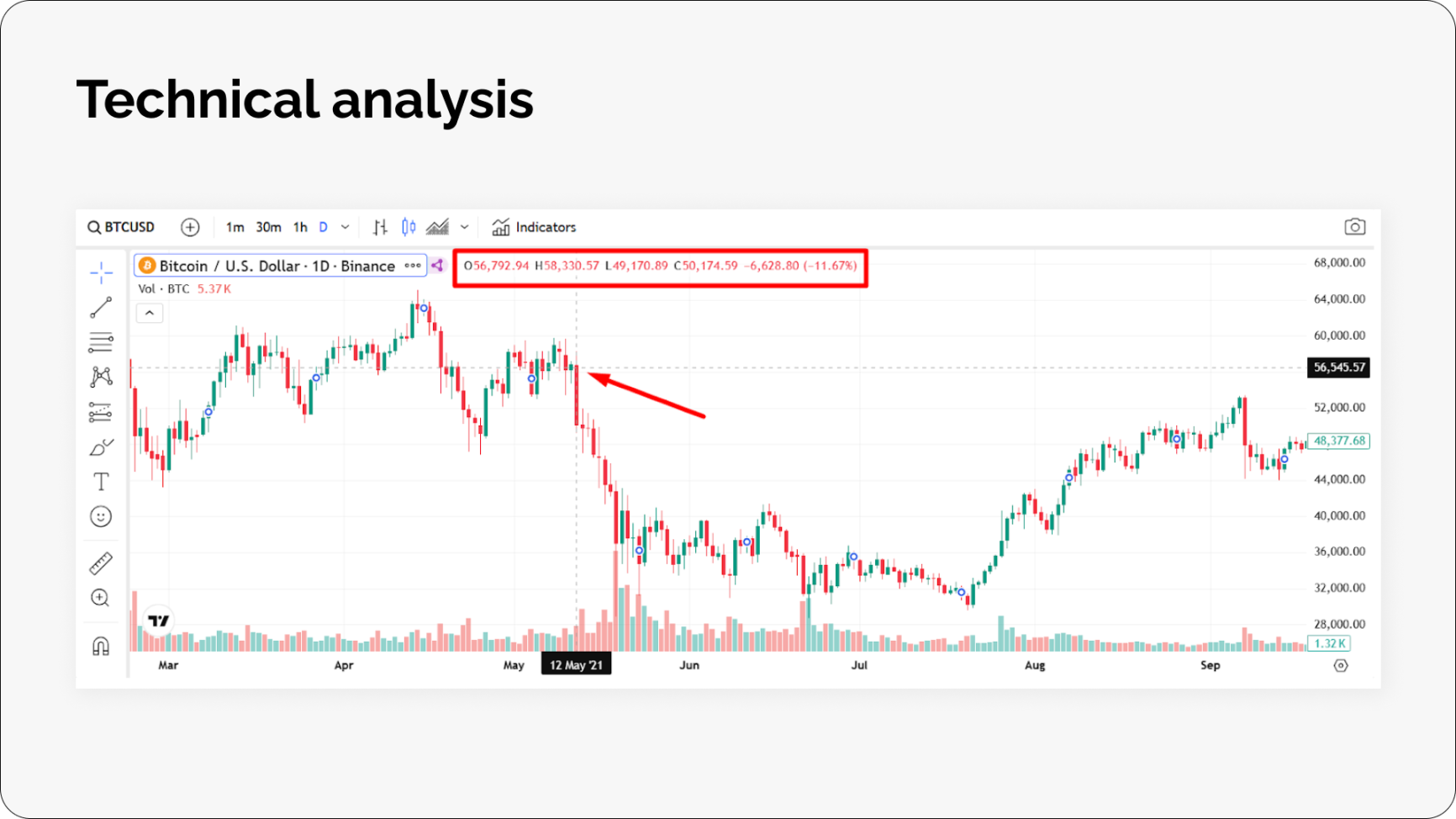
Tesla’s decision to stop accepting Bitcoin in 2021 and a tweet from Elon Musk led to an immediate 12% drop in Bitcoin’s price. Credit: Coinspaid
As briefly mentioned before, crypto is uniquely vulnerable to FUD: it trades 24/7, moves fast, and lives on social distribution. A rumor can spread, trigger leverage liquidations, and wipe out market cap before most people can even check the primary source.
Market Impact
With the exception of edge cases, the FUD propagation chain and effects are generally consistent:
- A rumor or alarming headline appears (anonymous sources, edited screenshots, ambiguous regulatory language).
- It spreads through Crypto Twitter, Telegram, Discord, and on-chain monitoring accounts that frame selective wallet movements as “confirmation.”
- Traders react: market sells hit order books, stop-losses cascade, desks de-risk, and appeal to fear becomes self-fulfilling.
- Market effects show up quickly.
Common measurable signals that traders can use to confirm FUD spreading include volatility expansion (Bollinger Bands/ATR), funding rates flipping negative, spreads widening, liquidation spikes, stablecoin exchange flows, and thinning order books.
The time horizon can vary a lot, too. Unverified claims often create intraday wicks that recover once the rumor is debunked or fails to catch on. Multi-day drawdowns appear when uncertainty lingers (audits, probes). Long-term repricing happens when the “FUD” is actually a verified fundamental negative.
How It Affects Investors
FUD impacts markets through price dynamics and behavioral shifts.
On the price side, FUD drives volatility spikes and wider spreads as market makers price in information asymmetry risk. Rumors about earnings, probes, or liquidity issues can trigger algorithmic de-risking before humans even read the underlying claim.
The effects are not the same for traders and less involved investors either. Day traders face tradable volatility but risk getting caught in debunked reversals. Swing traders face thesis drift when technical damage arrives before fundamental clarity. Long-term investors are tested on discipline—confusing temporary price impact with permanent value destruction is the real danger.
A helpful anchor is the difference between signals (anonymous posts, influencer claims without docs, unusual volume, secondary headlines) and evidence (SEC filings (10-K, 10-Q, 8-K), audited statements, official regulator notices (SEC.gov, DOJ press releases), full earnings transcripts). Evidence is accountable and verifiable. Signals might be right, but they’re not confirmable at the moment they spread.
How to Identify FUD and Verify Claims
Spotting FUD is not always self-evident and is mostly about pattern recognition: how claims are framed, what evidence is included (or missing), and how the narrative spreads.
Before you make a decisive conclusion, you might want to separate FUD vs. Legitimate Critique. A few tests clarify most cases:
- Falsifiability: can it be tested and disproven?
- Source transparency: are sources named, dated, and verifiable?
- Appropriate specificity: does it target concrete mechanisms, not vague character attacks?
Also watch willingness to update. Good-faith critics revise when new data appears; FUD producers repeat and pivot.
A good verification workflow is like a wallet security routine: simple, repeatable, and hard to bypass when emotions run high.

Image by pikisuperstar on Freepik
Step-by-Step Verification
- Step 1: Claim extraction and isolation. Turn the message into 1–3 testable statements.
- Step 2: Identify claim type and evidence standard. Technical, financial, regulatory, team accusation—each needs different proof.
- Step 3: Locate primary sources. GitHub, official announcements, blockchain data, audits, filings.
- Step 4: Apply the source quality rubric. Use the scoring criteria below.
- Step 5: Cross-reference independent sources. Confirm with unaffiliated validators.
- Step 6: Reconstruct context. Look for missing timelines, conditions, and offsetting facts.
- Step 7: Test the counterfactual. What would disprove it? If nothing can, it’s unfalsifiable.
- Step 8: Document your conclusion with confidence levels. True, False, Misleading, or Unverifiable—and what would change your mind.
| FUD Signal | Example | Verification Method |
|---|---|---|
| Loaded language & emotional appeals | “Reckless developers gambling with user funds…” | Strip adjectives; verify the factual core independently |
| Cherry-picked charts or timeframes | Highlighting a 40% drop while ignoring the prior month’s gains | Pull full historical data; check base rates and representativeness |
| Anonymous “experts say” claims | “Industry veterans confirm…” with no names, dates, or bodies involved. | Search for the primary statement; look for named experts saying the same |
| False urgency or artificial deadlines | “Sell everything NOW or lose 90%” | Check whether the timeline is event-driven or arbitrary |
| Vague technical accusations | “Recursive vulnerability in the merkle tree validation layer” for a system that doesn’t use merkle trees. | Locate the exact code/function; consult developers/auditors |
| Conspiracy theories about team intentions | “Secretly planning to abandon the project” | Check on-chain behavior, GitHub commits, treasury moves, communications |
| False dilemmas (“only two options”) | “Sell everything NOW or lose 90%” | Enumerate alternative scenarios the claim ignores |
| Misrepresented statistics | “Urgent: massive outflows detected...” | Find original dataset; validate sample size and methodology |
| Screenshot as evidence | Reverse image search; validate interface/timestamp; find original post | |
| “Breaking” unconfirmed reports | “This protocol will absolutely collapse within 48 hours.” | Check official channels and reputable outlets; wait 2–4 hours before sharing |
Amplifying FUD While Verifying
One pitfall that anyone can stumble onto while meaning well is accidentally amplifying FUD. For example, even if you are trying to debunk an unverified claim in a quote-tweet or share in any other way, you are still boosting its reach. Or, once isolated, screenshots become easy to weaponize and manipulate, so saving and archiving is best done with the full context.
What you can do to remedy these effects is separate analysis from distribution by addressing it publicly and paraphrasing instead of embedding the claim and state any uncertainty clearly.
Another tip that can help is to timebox the process not to get carried away nor miss any inconsistencies. 30–60 minutes is enough for most claims; update later if new evidence arrives.
Identifying FUD is probabilistic pattern recognition, not a diagnosis of intent. Claims can be wrong due to misunderstanding, outdated info, or honest error. Use evidence-based phrasing (“unsupported by available evidence”) rather than accusing “lying” or “intentional disinformation.” Defamation risk is real—focus on claim accuracy and evidence quality, not motives.
Risks of Fear, Uncertainty, Doubt

Photo by Treddy Chen on Unsplash
FUD becomes a genuine risk factor when it crosses from skeptical questioning into coordinated manipulation. The three practical indicators are: intent, evidence quality, and distribution method. When those align toward manufactured uncertainty—especially via coordinated amplification and loaded language—FUD stops being noise and becomes a strategic weapon.
FUD-driven market manipulation tends to follow the same sequence: a rumor is created, selective framing emerges and gets amplified, the short-term impact arrives in volatility and liquidity, and then the FYD settles in.
Watch for coordinated cadence, identical phrasing across “independent” accounts, timing around catalysts, and anonymous sourcing without artifacts.
Also keep the distinction sharp: misinformation is false info shared without malicious intent. Disinformation, however, is false or distorted info shared with an express intent to deceive and manipulate. Misinformation can be corrected; disinformation requires containment and defensive process.
Other risks FUD posits to projects are erosion of trust or spawning the narratives that outlive any rumor. It can have an operational or organizational impact and even become legally actionable. However, no matter how effective, it can be countered with the exact opposite of the response it seeks to elicit.
How to Respond to FUD
The best response is systematic: move fast enough to protect yourself or your users, but slow enough to stay accurate—and avoid giving propaganda free distribution. So, avoid amplification, separate claims from emotion, stick to primary sources, and limit the time you are exposed to the FUD.
A simple six-step workflow keeps you grounded.
- Pause and classify the FUD type. Is it fear, uncertainty, or doubt? While you are analyzing it, you can come up with more effective countermeasures and slow down for a bit to help you shift from emotional response to productive action.
- Verify with a structured checklist. Source, context, date, incentives, corroboration.
- Choose engagement level. Ignore, ask clarifying questions, or correct publicly (rare).
- Respond calmly with evidence. Acknowledge → correct → provide evidence → state next step.
- Protect downside through decision hygiene. Sensible position sizing, alerts for review (not panic actions), limited exposure to FUD channels.
- Track outcomes. Build your own pattern database for sources and narratives.
| Do | Don't |
|---|---|
| Archive sources with timestamps | Quote-tweet misinformation to “debunk” it |
| Verify with multiple independent primary sources | Debate anonymous bad-faith accounts |
| Ask specific questions that force clarity | Use ad hominem attacks |
| Correct once with evidence, then disengage | Move goalposts after a debunk |
| Report coordinated disinformation | Doom-scroll for hours |
Conclusion
FUD changes decisions by shifting attention from evidence to emotion, replacing verifiable claims with vague dread that feels urgent but resists correction. At the same time, not every warning is FUD. Legitimate risk communication cites falsifiable evidence, offers mitigation steps, and invites scrutiny rather than demanding immediate belief. When a message meets those criteria, dismissing it as FUD becomes an irrational move.
How do you feel about FUD? Let us and other crypto enthusiasts know in the comments on our social networks: X, Facebook, and Telegram! Stay tuned to updates from the crypto market and explore other digital assets in the ChangeHero blog.
Frequently Asked Questions
Who typically spreads FUD in crypto markets?
Competitors, short-sellers, and ecosystem rivals deploy FUD to suppress token prices or redirect attention. In traditional markets, short-sellers amplify negative narratives to profit from declines, while in crypto, rival protocol communities may highlight risks in competing chains to attract developers and liquidity.
What’s the difference between spreading FUD and amplifying it?
The creator manufactures the narrative with deliberate intent, while amplifiers—often well-meaning—share it as a warning. The target still pays the cost in volatility and reputational damage, whether the original intent was malicious or not.
Can FUD be accidental, or is it always deliberate?
It can be accidental—misread docs, incomplete disclosures, panic speculation. The difference is correction behavior: accidental FUD tends to fade when facts appear; deliberate campaigns persist, pivot, and intensify despite counter-evidence.
Do influencers and community moderators ever use FUD for engagement?
Yes. Some influencers lean on controlled FUD to drive engagement and position themselves as “protective authorities.” Some moderators weaponize the “FUD” label to silence legitimate critique.
How do political campaigns and litigants employ FUD outside financial markets?
Political operatives frame debates around maximized threat scenarios to mobilize voters. Litigants may use uncertainty around liability or regulatory interpretation to pressure settlements. Both rely on emotional urgency over evidentiary completeness.
Why does the term FUD matter beyond being crypto slang?
Because calling something “FUD” can shut down inquiry without addressing evidence. Understanding the tactic helps you avoid both over-reacting to manipulation and under-reacting to real risks.
Why doesn’t calling something “FUD” count as a refutation?
Refutation requires counter-evidence. Labeling something as FUD comments on tone or intent, not truth value. The real questions are: what would disprove it, and what independent sources confirm it?
When is FUD useful versus harmful?
Useful FUD surfaces verifiable risks and invites verification. Harmful FUD relies on fabrication, selective omission, and emotional escalation while resisting falsification.
How does recognizing FUD improve reputational risk management?
It helps teams allocate resources correctly: address substantive concerns transparently, and avoid reactive engagement that amplifies manipulative narratives.
What separates FUD from legitimate concern?
Primary sources, verifiable trails (transaction hashes, timestamped comms), reproducible technical demonstrations. FUD leans on vague “sources say” and theoretical scenarios framed as certainty.
What do source incentives reveal about spreading FUD?
Financial positions, competitive stakes, anonymity, and historical accuracy all matter. High emotional intensity paired with poor accuracy is a classic FUD signature.
How does timing context distinguish panic from pattern?
FUD clusters around catalysts—token unlocks, launches, comment periods. Legitimate concerns emerge across time and evolve proportionately.
How does FUD differ from disinformation?
Propaganda tends to be broader and institutionally coordinated; FUD is often tactical suppression or market manipulation. Misinformation lacks malicious intent; FUD is typically deliberate. FOMO drives approach behavior; FUD drives avoidance. In extreme environments, repeated FUD can resemble indoctrination; open-source voices like Eric S. Raymond have discussed narrative warfare around Linux and enterprise distributions like Red Hat as part of how perceptions are shaped alongside technical merit.